RADIUS Accounting Best Practices
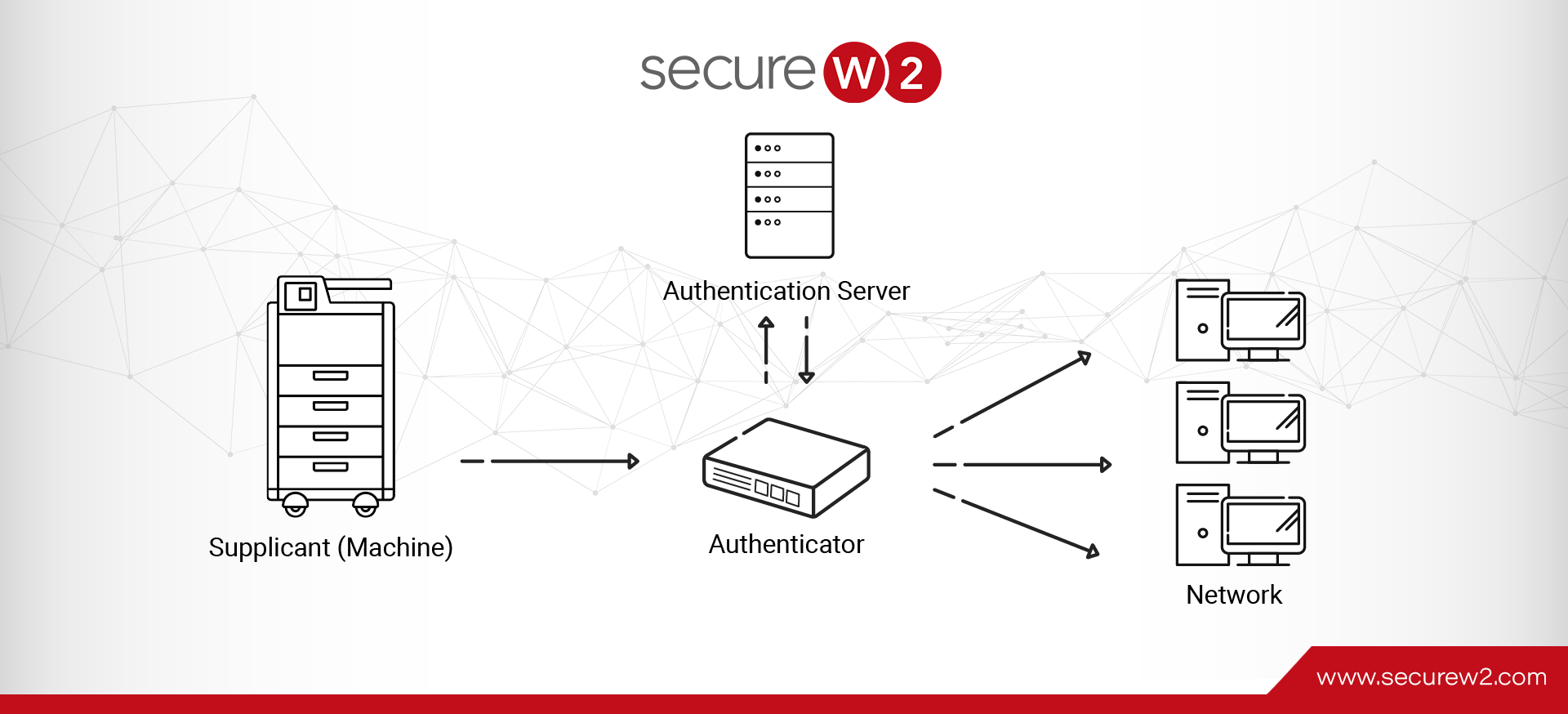
RADIUS is a crucial networking protocol best known for centralized authentication, authorization, and accounting (AAA) administration. The final “A” in AAA signifies accounting, a fundamental aspect of network management. Network Access Servers (NAS) typically function as clients and manage user ... Read More