What is Over-the-Air Credential Theft?
Over-the-air credential theft occurs when someone spoofs an SSID within the physical vicinity of devices that are configured to connect to that SSID, causing devices to send their credentials to the spoofed SSID instead of the legitimate one. According to the 2018 Credential Spill Report, an average of 1 million credentials were exposed daily in 2017, with no indication that this number will decrease.
How Do I Prevent Over-the-Air Credential Theft?
Offer Technology for Easy Configuration
An area of vulnerability for over-the-air credential theft is when users manually configure their devices for WPA2-Enterprise. When users omit a few difficult-to-configure settings, such as RADIUS certificate installation, they lose all the security benefits of WPA2-Enterprise and are susceptible to over-the-air credential theft. Providing onboarding/configuration technology to network users not only creates a better user experience, but it also significantly reduces the risk of over-the-air credential theft.
Replace Passwords with Certificates
While utilizing onboarding/configuration technology can minimize risks for over-the-air credential theft, they are not foolproof since users can choose not to utilize them. Using certificate-driven security guarantees that users go through an enrollment process that ensures their devices are properly configured and organizations can rest assured that privacy is protected.
As an organization we had an initiative to move everything to the cloud. SecureW2 allowed us to remove our reliance on AD, and use our Azure AD directly for our Wi-Fi and VPN authentication.
IT MANAGER
Configure Device for Server Certificate Validation
Server certificate validation prevents over-the-air credential theft by configuring devices to validate the identity of the SSID’s server before sending credentials.This security measure is often overlooked for two primary reasons: the organization does not know about it, and it’s difficult for end users to configure. Misconfiguring server certificate validation is easy, especially since devices can be misconfigured and still connect to the network, which negates the security benefits of WPA2-Enterprise. Manually configuring it on Windows devices, shown in the video, takes 14 steps.
Everything Needed for Certificate-Based Authentication
We provide everything an organization needs to deploy EAP-TLS, certificate-based 802.1X for Wi-Fi security. The #1 rated onboarding client to enroll certificates, certificate management tools, managed device auto-enrollment gateways, a RADIUS server and much more is included in the SecureW2 solution. Plus, we're vendor neutral. You can plug and play any part of our solution, so there's no need to forklift your existing network infrastructure.
Configuration Client
Starting with a great end user experience, the JoinNow Suite provides customizable and adaptable onboarding clients that set up devices for Wi-Fi, VPN, Web and SSL Inspection security. JoinNow takes the frustration out of delivering secure networks by delivering all turnkey backend services for device enrollment, authentication and management. In an age where BYOD, IoT, and managed devices reign, our technology provides the answers by leveraging the components you currently own.
Powerful Certificate Management and Configuration Features
Remotely Troubleshoot Devices
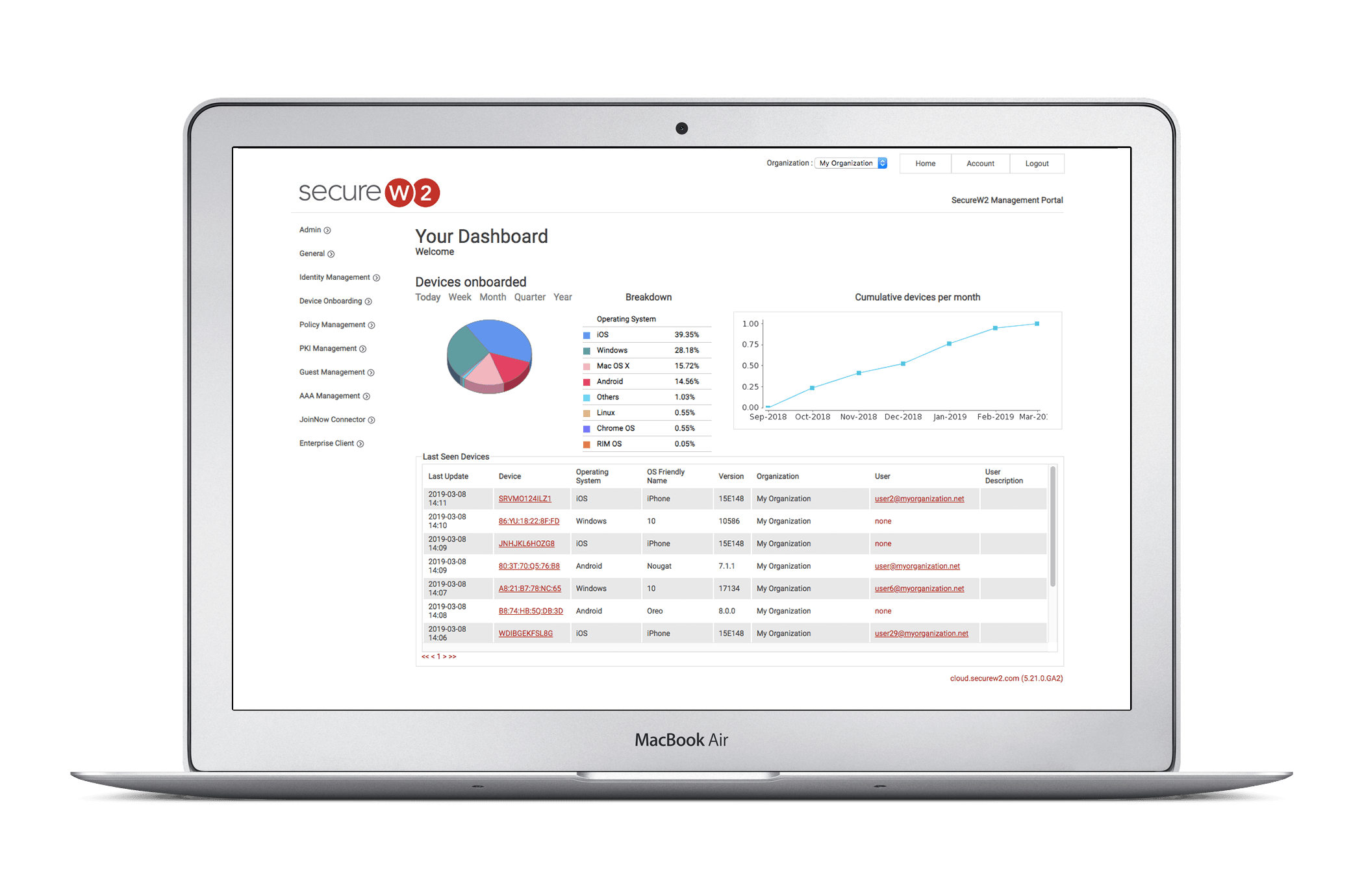
SecureW2 software allows you to troubleshoot errors in real-time with individual devices and monitor network connections. View and fingerprint which devices are connecting to the network while they are being onboarded, and simultaneously monitor any connection messages users may encounter. Detailed information about individual devices such as network adapters, MAC addresses, driver versions, and manufacturer and driver dates help network admins begin the troubleshooting process and gather analytics from the cloud. End-user data including device type, operating system/build version, and application version is securely reported back to the cloud and made available for network admins for use in assessing connection patterns and creating network visibility.
Configure Server Certificate Validation
Server certificate validation is one of the most important ways of preventing over-the-air credential theft. Manually configuring server certificate validation isn’t supported by Apple devices, and is very difficult to do on Android and Windows devices. SecureW2’s onboarding client ensures that devices of all operating systems are configured for server certificate validation when they are setup for network access.
Create Robust Certificate Policies
SecureW2 makes it easy to track and manage certificates. Certificate policies allow the administrator to determine the lifecycle and permissions of client certificates, as well as automated notifications to users, administrators, and external systems regarding the issuance, revocation, and expiration of certificates. For example, you could create a policy that gives students certificates with a 4-year expiration, and staff an 8-year expiration.
Revoke User Access After They Leave
SecureW2 comes with a built-in CRL (Certificate Revocation List) and provides mechanisms to validate current user status in the organization. Network administrators can also manually delete certificates from the management portal at any time. You can rest easy knowing that only current members of the organization have access to the network.
Over-the-Air Credential Theft FAQs
How Can Certificate-Based Authentication Prevent Credential Theft?
Certificate-based authentication (CBA) uses digital certificates which are based on public-private key encryption. This encryption ensures that the information sent over-the-air is protected from the view of unauthorized third parties.
Certificates can also be used as a replacement for passwords in Wi-Fi access, application access, and more. Tying digital certificates to the identity of users and devices adds an extra layer of security by preventing the identity theft associated with the credentials.
If you’re not sending passwords over-the-air, then there aren’t any passwords to intercept and take.
Additionally, certificate-based authentication prevents password mismanagement, such as weak passwords, misplacement of passwords, and so on. Reduction in password mismanagement naturally protects users from credential theft.
How Can Credential Theft Attacks Occur Over Wi-Fi?
Threat actors can steal login credentials over Wi-Fi through a number of attack vectors. Examples of attacks that can lead to stolen credentials over Wi-Fi include spoofed SSIDs, man-in-the-middle (MITM) attacks, evil twin attacks, brute force attacks, social engineering, phishing emails, and more. These credential theft attacks can target both corporate users and consumers in large-scale credential harvesting.
Sometimes, the hacker uses techniques like DNS spoofing to gain access to user credentials, where they create an illegitimate web page or malicious software that seems authentic and redirect traffic there. When new users enter their corporate credentials or individual user credentials on the fake web page, they are transmitted right away to the hacker, making them susceptible to corporate credential theft and consumer credential theft. The hackers utilize these stolen credentials to gain unauthorized access to their critical data over the air.
How Can PKI Protect Against Credential Theft or Stolen Credentials?
A PKI (Public Key Infrastructure) is a framework that manages digital certificates, which are one of the greatest security defenses available to prevent credential theft. A PKI allows organizations to issue, revoke, and otherwise manage each certificate.
Because digital certificates can replace credentials in a variety of ways, they can stop hackers from stealing credentials for a number of critical resources. Certificates can prevent credential theft attacks for Wi-Fi credentials and cloud application credentials. They can even prevent stolen credentials from desktop logins.
Another common cause that allows hackers to steal credentials is password mismanagement. Users often recycle passwords or create weak passwords that malicious software can easily steal. By enabling certificate-based authentication with a PKI, administrators no longer need to worry about login credentials being vulnerable to password mismanagement.
What Is the Passwordless Authentication Experience Like for the End User?
The passwordless authentication experience for an end user is much more seamless and secure compared to traditional passwords. Passwordless authentication comes in various forms, such as Multi-Factor Authentication (MFA), Two-factor authentication, biometric authentication, or one-time passcodes received via SMS or email. One of the most secure forms of passwordless authentication is certificate-based authentication(CBA), which uses digital certificates to authenticate and can be combined with two-factor authentication.
Digital certificates work on the principle of asymmetric encryption and hence minimize almost all the risks associated with credential-based attacks, making them one of the most secure authentication methods. While the experience can vary slightly based on what users log into, it generally involves choosing their certificate at the time of authentication.
For something like Wi-Fi, end users usually have no idea a certificate is being used. Managed Devices can have certificates automatically configured for Wi-Fi using most MDMs, and 802.1x Onboarding platforms like SecureW2 configure unmanaged devices for passwordless authentication. Most users don’t even notice the difference.
Can’t Hackers Just Export the Certificate’s Private Key and Use That to Gain Access to Other Devices?
Certificates are based on the concept of asymmetric encryption, which uses both a public and private key for safe encryption and decryption. The private key is integral. If threat actors don’t have the private key, they won’t be able to do anything with the certificate.
One of the greatest security measures for private key protection is to make sure they are stored in the proper places on devices. We recommend storing them in the correct key store and secure enclaves, as well as setting the private keys to non-exportable at the time of issuance. If the device has a Trusted Platform Module (TPM), storing the private keys there further enhances security. PKIs like SecureW2 can attest that private keys have been generated in hardware like TPMs and Secure Enclaves and can also configure private keys as non-exportable.
Schedule a demo
Sign up for a quick demonstration and see how SecureW2 can make your organization simpler, faster, and more secure.
Pricing Information
Our solutions scale to fit you. We have affordable options for organizations of any size. Click here to see our pricing.