We are living in a time where wireless security is imperative because private data and personal information are uploaded online. As the amount of online data increases, so does the monetary cost of cybercrime. Cyber crime is now the most prevalent crime in the country with a person 20 times more likely to become a victim than suffer robbery and ten times more likely to be defrauded than to suffer theft.
Organizations have to secure their data by protecting its digital assets, including server access, user authentication, and safe communication protocols.
Any organization that still authenticates users with passwords is sending their data through CLEARTEXT, which is as easy to read as the article. Organizations can easily fall prey to all kinds of cyber attacks, including phishing attacks, social engineering attacks, and the infamous man-in-the-middle attack. Sensitive data sent and stored in clear will be compromised.
Public-key encryption is the best option for authenticating users with digital x.509 certificates. SecureW2 offers a turnkey PKI that admins can set up with no forklift upgrades required, check out what one of our customers has to say.
Here we will explore how cryptography works, the importance of public and private keys, the relation of keys to Public Key Infrastructures (PKI), and how to manage identity and secure communication over the Internet.
What is Public Key Encryption?

Public key encryption is a method to protect information that’s either shared through an open channel on the web or stored in a device or on the cloud. It’s based on a one-way function, or a function that is easy to compute, but difficult to invert. One way functions used in public key cryptography allows us to define the two keys used to encrypt and decrypt the information.
This method is also known as asymmetric encryption, as opposed to the more vulnerable symmetric encryption, which only relies on a shared key. In asymmetric encryption, one key encrypts and the other decrypts, implementing a stronger security measure than just one key that does both.
The public key will be shared to encrypt data, anyone can send data encrypted to the recipient using the public key (and why it’s called “public”), but only the private key owner will be able to decrypt. In this sense, we don’t want anyone to learn the private key from the public key.
Public key cryptography is widely used today for securing web traffic and for network security protocols. It puts the “S” in “HTTPS”.
What about Private Key Encryption?
Private key encryption, or symmetric cryptography, uses the same key to encrypt and decrypt data. The security of this kind of cryptosystem relies heavily on the key management and the key length, the longer the key the safer the cryptosystem.
Today’s encryption algorithms are hybrid cryptosystems, using both symmetric and asymmetric encryption. For the most part, private key encryption is used to securely share keys generated by a public-key protocol.
Public Keys vs Private Keys
A public key is made available to the public so other parties can use it to encrypt messages they want sent to that public key owner. As long as you keep your private key safe, you can allow others to use your public key without you having to compromise any security.
Since the key is public, other parties can send their encrypted messages to the key owner. It’s imperative that an attacker not obtain the private key from the public key. This is why all public-key cryptosystems are based on a difficult mathematical problem, with high computational complexity.
The security of a cryptosystem relies on the private key being kept secret, both when it’s generated and stored. The random numbers used for the algorithms in cryptography must be difficult to guess, that’s why it is not a good option to rely only on software development for the key generation algorithm.
Programs are not good for generating truly random numbers, it only can achieve a pseudo-randomness, which is not secure. It is recommended to use hardware devices, like a Hardware Security Module (HSM), for generating and storing the private keys, where it can be achieved a higher level of randomness.
Public Keys and Digital Certificates
Public key cryptography allows organizations to issue certificates and verify a user’s identity with a digital signature. In this case, the keys have a different function from that of encrypting and decrypting.
In a digital signature, the private key has the responsibility for digitally signing documents and authenticating the identity. The public key is meant to verify the signature and verify the authentication.
Digital certificates are cryptographic documents that can serve as a user ID for authentication purposes. Certificate Authorities (CA) serve as the trusted agent to publish public keys that are linked to private keys of approved network users. CAs create certificates by signing certificate signing requests (CSR) with its private key.
Users can present their credentials with their public key and the authority will generate a certificate, input their credentials, sign it with its private key, and the user is now given an approved certificate.
When a user wants to encrypt a message, the CA ensures they are using the right public key and the message will get to its intended target. CAs also signed digital certificates, stamping them with a mark of approval so they can be equipped onto network devices and simplify user authentication.
A PKI is a setup where users’ public keys are stored on public servers and made available in an online directory. PKIs handle the issuance, management, revocation, and distribution of digital certificates, just to name a few. Digital certificates and CAs make up part of the PKI and need it to operate effectively.
SecureW2 offers a Managed Cloud PKI, a turnkey solution that provides an organization everything they need to leverage Public Key Encryption for their network security. Easily generate your own CAs and Certificate Revocation Lists, issue custom certificates through our robust policy engine, create auto-enrollment APIs, and much more.
SecureW2 is also ISO 27001 certified and backed by a powerful HSM to keep your private keys locked tight. SecureW2’s PKI also offers the only last mile certificate delivery platform, as users can use our software to self-service themselves and install certificates for BYODs, Managed devices, smart cards, IoTs, and email clients.
How Public Key Encryption Works
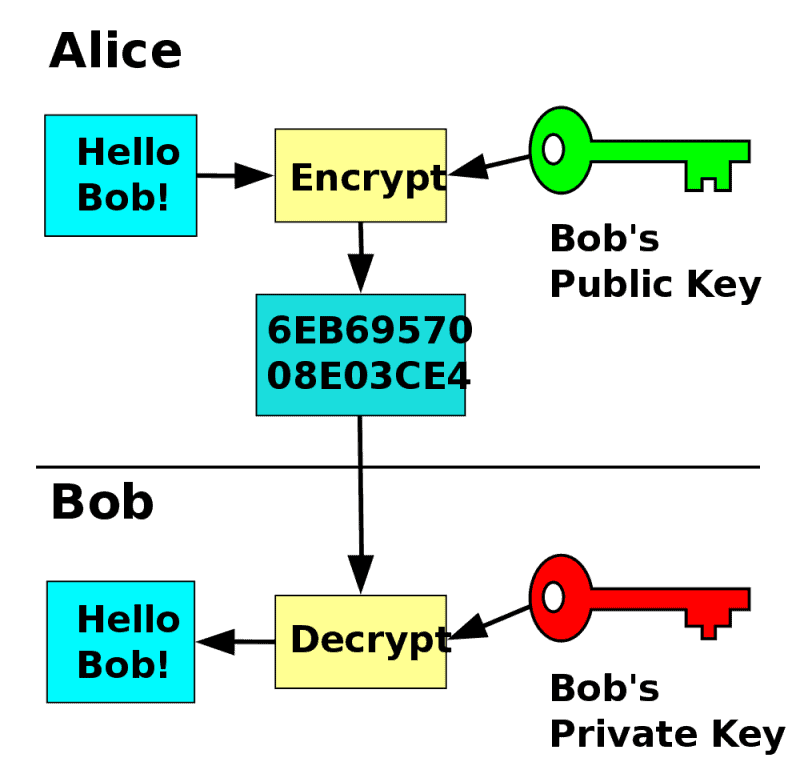
If a public key encrypts the message, only the private key will be able to decrypt and access the message and vice versa.
The best analogy for public key encryption is the Bob-Alice trunk example, introduced by Panayotis Vryonis:
Two people, Bob and Alice, use a trunk to exchange messages. The trunk has a lock that only Bob and Alice can access. If Bob and Alice use the same key to lock and unlock the trunk, that explains symmetric encryption. There are just two states of the trunk, locked and unlocked.
However, asymmetric encryption incorporates a third state.
- Locked on the left.
- Unlocked in the middle.
- Locked on the right.
The process requires the use of two keys (public/private key pair). One key can only turn to the left side, while the other key can only turn to the right side. Both keys can lock the trunk, but whatever key you used to lock the trunk, only the other key can unlock it.
Alice can now pick one of the keys to be shared on the network, making it the “public” key and keeping the other one to herself, “private”. Bob can place a message inside the trunk and lock it with Alice’s public key(turning it all the way to the left), confident that only Alice can unlock the trunk and read the message.
Also, Alice can send a message back to Bob by locking it with her private key (turning it all the way to the right). Bob can verify Alice’s identity because only her private key has the ability to lock the trunk on the right side, guaranteeing that the message is from her.
Switch out the trunk with plaintext data and the physical keys with cryptographic keys and that’s the basics of public key cryptography.
In a digital space, one can write out a message in plaintext, or unencrypted data, and combine with a key to create a ciphertext, or encrypted data, which looks like a long string of random letters and numbers, confusing to the naked eye. The other key in the key pair can take this random string of data and turn it back into plaintext, allowing the user to read the message unencrypted.
- Plaintext + key = ciphertext
- Ciphertext + other key = plaintext
Another function of public key cryptography is the digital signature. We briefly touched on this back in the Bob-Alice analogy, the digital signature allows recipients of messages to verify that the message is legit and the sender is who they say they are.
The sender signs the message with their private key, creating the digital signature.
Here’s a quick overview of how it can be done:
- Use a hash algorithm, more specifically a one-way hash function, to turn your message into a hash, a condensed version of the message.
- Encrypt the hash with your private key, or sign the message, so the recipient can decrypt with your public key.
- The hash can be combined with a user’s public key to create a digital signature. Now, if someone receives a message from them, the recipient can ensure the message is legit.
- Once the recipient verifies your identity, they can decrypt the message with your public key and access the message.
Is Public Key Encryption Secure?
While private key encryption can be accomplished more quickly, public key encryption is more secure because incorporating two keys instead of one key provides stronger security measures.
If the shared private key were to be lost or forgotten, users will not be able to encrypt or decrypt messages. If the shared key is stolen, the entire system is compromised.
Asymmetric encryption is designed to be complex, strengthening security measures. Messages encrypted with a public key can only be decrypted with the corresponding private key, which is only accessible to the owner.
Digital certificates also increase security because they themselves are encrypted, meaning if they were to fall into the wrong hands, the certificate is still impenetrable.
Public key encryption gives responsibility to the user on how to manage the private key, because compromising the private key could lead to the data leak, user impersonation, or misusing of the digital certificates.
How SSL/TLS Uses Public Key Encryption

Public key cryptography is vital for Secure Sockets Layer (SSL) and Transport Layer Security (TLS), which are themselves vital for secure HTTPS web browsing. Websites have SSL/TLS certificates containing the public key, while the private key is installed on the website’s origin server, or CA.
SSL certificates are a vital part of the TLS “handshake”. When a browser initiates the handshake with a web server, the server sends it’s SSL certificate so the browser can verify the server’s identity by checking the CA that issued the certificate.
Digital certificates authenticate using the EAP-TLS authentication protocol, which is the most secure option when compared to other authentication protocols. EAP-TLS uses the TLS public key authentication mechanism in EAP, meaning both client and server can verify each other before starting the authentication process.
How to Generate a Public/Private Key Pair
Each public-key cryptosystem includes an algorithm to generate the keys. The algorithm on which the cryptosystem is supported provides a process to generate the public and private key pair.
There are several algorithms you can use to generate a public/private key pair, but we will discuss three main cryptosystems.
The RSA Algorithm
The Rivest-Shamir-Adleman algorithm is one of the original public key cryptosystems and still the most widely used public key cryptography algorithm. RSA is widely used because of its ability to distribute public keys and provide digital signatures. RSA is well-known for its strong security because it factors large integers that are nearly impossible to guess.
Theoretically, an attacker would have to try to factorize the large integer to find the private key and guess the random elements added in the key generation.
The DSA Algorithm
The Digital Signature Algorithm does exactly what it’s named after, creating digital signatures.
DSA was proposed in 1991 by the National Institute of Standards and Technology and is the standard for government agencies, while RSA is used more in the private sector.
DSA was introduced after RSA and may seem like a downgrade because it can only do digital signatures and not public key encryption. However, both methods are very similar and both are lauded in regards to security. The differences lie in the arithmetic used and speed. DSA is a much faster signature, but RSA is better at verification. In the end, both RSA and DSA are pretty equal in terms of compatibility since they both use the same IPs and digital certificates.
Elliptic Curve Cryptosystem
Cryptographers quickly noticed the more complex the mathematics behind a cryptosystem, the more secure it is.
In search of better options, the Elliptic Curve has come across. It’s a mathematical structure that has been in the theoretical field of mathematics for many years. On it, we can also define the Discrete Logarithm Problem, but with numbers living in a curve. So the curve is part of the public key and some random number on the curve is the private key.
Safely Storing Private Keys in a PKI
So far, we’ve covered how important private keys are in public key encryption. Public keys don’t need to be stored anywhere since they’re available to the public, but private keys need to stay protected in order for the whole process to work.
With SecureW2, admins can use our industry-exclusive technology that prevents Private Keys from being exported from devices. This extra PKI security layer ensures certificates are never stolen or transferred from the device.
Certainly certificates need to be tied to devices, but what you really need for the best private key protection is an HSM. SecureW2’s PKI backs all Private Keys in an HSM, a crypto processing device and delivers strong encryption and security benefits. HSMs are designed to protect and manage all private keys in the network. On the key management side, the HSM oversees the complete lifecycle of private keys, including creation, rotation, deletion, auditing, and API integration support.
How to Recover a Private Key
There are several reasons for a private key to be missing, but the most common ways are either the certificate wasn’t installed on the server that generated the CSR, the certificate was installed incorrectly, or the request was outright deleted.
Private key recovery usually depends on the operating system your environment uses. Here’s a link that outlines how you can recover a private key for each OS.
Many organizations will use a key escrow to protect and easily recover cryptographic keys in case of an emergency, like a security breach or natural disaster. The private keys are stored in a trusted third party and the organization can set guidelines for the escrow service provider on who is allowed access to the keys.
Key escrows differ from a key recovery agent, which is a person authorized to recover a certificate for an end user. The recovery agent is usually a high-ranking member of the IT department and is permitted to decrypt a user’s encrypted data during an emergency. This forum post summed up the difference best, saying that a “key escrow is someone who holds the key for end users, while a recovery agent has the master key.”
Effective Public Key Encryption with a Managed PKI
Public key encryption strengthens wireless security because of its asymmetric key pairing. Sharing one private key that both encrypts and decrypts gets the job done more quickly, but is a massive security risk. The public/private key pairing ensures that only the right person will see the message and proves the identity of the key owner.
If you are interested in implementing Public Key Encryption on your network, consider SecureW2’s Managed PKI. Our PKI service allows you to have your own Private PKI at a fraction of the cost of setting it up on your own. It is entirely on the cloud, simplifies and secures user authentication, can be integrated into any environment, and comes at an affordable price.