Wi-Fi access has evolved from the manual selection of Service Set Identifiers (SSIDs) to the automated, secure connectivity of Passpoint. Initially, users had to browse a list of available SSIDs, select a network, and manually enter credentials—an often cumbersome and insecure process. Passpoint, developed by the Wi-Fi Alliance, revolutionizes this paradigm by enabling devices to discover and connect to Passpoint-enabled networks automatically using pre-configured profiles. This transition employs 802.1x authentication protocols for robust, secure connections and RADIUS servers for efficient credential management.
By eliminating the manual steps and automating network discovery and authentication, Passpoint significantly enhances user experience and network security, aligning Wi-Fi connectivity with a cellular network’s seamless, secure nature. This article discusses Passpoint and how it streamlines connecting to Wi-Fi networks, providing users with secure and automatic connectivity. We also discuss how Passpoint utilizes 802.1x protocols to ensure safe and authenticated connections, and lastly, highlight the importance of a robust authentication system, such as a Cloud RADIUS server, to support Passpoint-enabled networks.
What is Passpoint?
Passpoint, also known as Hotspot 2.0, is a cutting-edge Wi-Fi technology developed by the Wi-Fi Alliance to streamline and secure user connectivity in Wi-Fi networks. Designed for automated, seamless user experiences, Passpoint enables mobile devices to discover and connect to pre-configured Passpoint-enabled networks automatically. Using advanced protocols such as 802.1x for robust authentication and WPA2/WPA3 for encryption, Passpoint eliminates manual logins and reduces exposure to security risks. This technology could also leverage RADIUS servers to manage credential information, ensuring that only authenticated users gain access. By providing automated network discovery, secure connections, and seamless roaming, Passpoint revolutionizes how users interact with Wi-Fi networks, making connectivity as reliable and safe as cellular networks.
Passpoint Releases
Passpoint has been updated twice for a total of 3 Passpoint releases (referred to as r1, r2, and r3).
Passpoint r1 – The initial release of Passpoint established all of the essential features that characterize the technology, but the release’s focus was introducing Hotspot 2.0. Adopters could identify other Passpoint-enabled networks and automatically connect to the access point with the strongest signal.
Passpoint r2 – The first significant update to Passpoint improved many of the preexisting features. Still, it made the great leap of adding OSU, simplifying the onboarding process for end users, and standardizing credential management for the network.
Passpoint r3 – The latest update to Passpoint has continued to improve on its foundations while concentrating on security and liability and adding WPA3 support. An essential addition is a single SSID OSU support, which vastly simplifies the user experience.
There are also several new ANQP elements:
- Operator Icon Metadata
- Venue URL
- Advice of Charge
Another added functionality is implementing the Terms and Conditions pages into OSU. It seems like a step back from an end-user perspective, but it is a valuable shield against liability for the Passpoint service provider.
How Does Passpoint Work?
Passpoint is designed to automate discovering and connecting to Wi-Fi networks. Devices supporting Passpoint automatically identify and connect to Passpoint-enabled networks without user intervention. This is achieved through the following components:
- Automatic Network Discovery: Passpoint-enabled devices periodically scan for available networks and automatically identify Passpoint-enabled ones, eliminating the need for manual SSID selection.
- Pre-Configured Profiles: Devices come with pre-configured Passpoint profiles, which include credential information and network policies. These profiles enable the mobile device to recognize and authenticate to the appropriate network seamlessly.
- Secure Connection Establishment: When a device attempts to connect, it uses advanced encryption protocols, such as WPA2 or WPA3, to ensure a secure channel is established between the device and the network.
- Credential Management: Devices use secure methods to manage user credentials, ensuring that sensitive information used during the authentication process is protected.
- Seamless Roaming: Once authenticated, the device can seamlessly transition between different Passpoint-enabled networks and access points without requiring re-authentication, similar to the behavior of cellular networks.
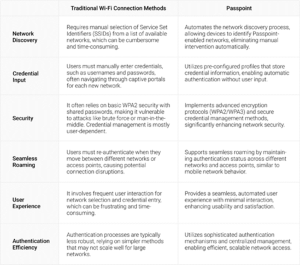
Passpoint vs. Traditional Wi-Fi Connection Methods
When comparing Passpoint with traditional Wi-Fi connection methods, several key points highlight the advantages and distinctions of Passpoint technology:
Passpoint and 802.1x Authentication
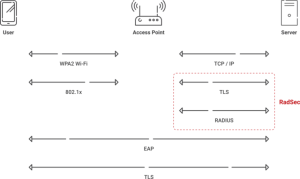
802.1x is an IEEE standard for port-based Network Access Control that provides an authentication framework for wired and wireless networks. It employs the EAP (Extensible Authentication Protocol) with a network access identifier to facilitate a secure exchange between a client device and an authentication server, often a RADIUS server. This protocol ensures that only authorized users and devices gain access to the network, leveraging various EAP methods, such as EAP-TLS (Transport Layer Security), to offer robust, certificate-based authentication.
How Passpoint Utilizes 802.1x Authentication
Passpoint incorporates 802.1x authentication protocols to fortify Wi-Fi network security and automate user connectivity. When a device attempts to connect to a Passpoint-enabled network, it initiates an 802.1x authentication process using pre-configured profiles containing EAP credentials. The device and network perform mutual authentication via an EAP method, like EAP-TLS, ensuring the client and network are trusted entities. This process involves verifying digital certificates stored on the device and the RADIUS server, providing a secure, encrypted connection is established. By integrating 802.1x, Passpoint eliminates the need for manual credential entry, automates secure access, and maintains continuous, authenticated connections, enhancing security and user experience across Wi-Fi networks.
Benefits of Passpoint Networks
Passpoint-enabled networks present the following advantages:
Enhancing User Experience with Passpoint
Passpoint significantly enhances user experience by automating Wi-Fi connectivity, eliminating the need for manual network selection and credential entry. Users benefit from a seamless connection process, where device profiles automatically discover and connect to Passpoint-enabled networks. This automation reduces user frustration and ensures seamless connectivity, which is particularly valuable in airports, conferences, and public venues.
Improving Wi-Fi Security through Automatic Authentication
One key advantage of a passpoint network is the robust security provided through automatic authentication. By leveraging advanced protocols like 802.1x and WPA2/WPA3 encryption, Passpoint ensures that all connections are authenticated and secure. This reduces the risk of unauthorized access, man-in-the-middle attacks, and data breaches, enhancing the overall security posture of Wi-Fi networks. Certificate-based EAP methods, such as EAP-TLS, ensure that only trusted devices and users can access the network.
Simplifying Wi-Fi Access for End Users
Passpoint simplifies Wi-Fi access for end users by automating the entire connection process. Pre-configured profiles on Passpoint-enabled devices handle authentication and network policies, eliminating the need for users to enter credentials or navigate through captive portals repeatedly. This streamlined access is particularly beneficial for mobile users who frequently transition between different Wi-Fi networks and access points, offering a hassle-free and consistent connectivity experience.
How to Deploy Passpoints in Existing Wi-Fi Networks
Deploying Passpoint in existing Wi-Fi networks requires a combination of hardware upgrades, careful configuration, and ongoing management to provide users with enhanced security and a seamless Wi-Fi experience. Here’s a step-by-step process for network administrators:
Step 1: Evaluate Current Infrastructure
Conduct a thorough assessment of the existing Wi-Fi network to determine compatibility with Passpoint technology. Identify access points and network components that need upgrades or replacements to support Passpoint features.
Step 2: Upgrade Access Points
Ensure access points (APs) are Passpoint-enabled by updating firmware or replacing outdated hardware. APs must support advanced Passpoint features, including automatic network discovery and secure authentication protocols.
Step 3: Create and Configure Passpoint Profiles
Develop profiles containing credential information, network policies, and certificate details. To enable automatic authentication and seamless connectivity, these profiles must be pre-configured on client devices.
Step 4: Establish Secure Credential Management
Implement secure systems for managing user credentials and certificates. This includes generating, issuing, and revoking certificates as needed to maintain a high level of security.
Step 5: Test and Validate
Extensive testing must ensure that all components of the Passpoint implementation work correctly. Devices must be validated to automatically discover, authenticate, and connect to Passpoint-enabled networks without interruptions.
Step 6: Monitor and Optimize
Continuously monitor the network’s performance and security to identify any issues or vulnerabilities. Optimize configuration settings and make necessary adjustments to maintain seamless and secure connectivity.
How a Cloud RADIUS Server Can Support Passpoint-enabled Networks
RADIUS, also known as AAA servers, are authentication servers that provide a centralized means of authentication for wired and wireless networks. Essentially, they verify any authentication requests by checking with a corresponding directory, such as a cloud Identity Provider.
With the addition of the RadSec protocol, RADIUS servers are excellent at providing current industry standard authentication in roaming scenarios. RadSec provides increased security for communications with the RADIUS server, leading to an even more robust authentication experience for users on the move.
SecureW2’s Onboarding Solutions for Simplifying 802.1x Authentication and Passpoint Support
Participating in a roaming consortium, such as Passpoint, necessitates robust and secure authentication solutions. SecureW2’s Cloud RADIUS server, which supports RadSec, provides scalable and secure authentication for smooth network access. Implementing a Cloud RADIUS server centralizes credential management, enforces severe security regulations, and allows for safe, certificate-based network access, improving your network’s overall security posture. This is especially useful for Passpoint-enabled networks, which rely on continuous, authorized connections to deliver a consistent user experience. To improve network security and streamline management, SecureW2’s RADIUS authentication solutions provides a safe, passwordless authentication solution with real-time policy enforcement, seamless integration with leading cloud identity providers, and worldwide availability.
Additionally, SecureW2 provides JoinNow MultiOS, a solution that streamlines the configuration of unmanaged devices for 802.1X authentication, which is required for Passpoint’s automatic and secure connections. JoinNow MultiOS simplifies onboarding by ensuring that devices have the credentials to authenticate and connect to Passpoint-enabled networks instantly. Using these sophisticated technologies, you can improve network security, provide a smooth connectivity experience for end users, and easily manage secure Wi-Fi access.
Visit our pricing page to learn how our certificate solutions may improve your Passpoint-enabled network.