Organizations that seek out opportunities to improve the efficiency of their network should consider using SAML authentication to implement a Single Sign-On (SSO) policy.
First and foremost, SAML is an XML-based markup language for security assertions, or statements that service providers use to make access-control decisions. A simple analogy to understand it would be to think of the relationship of LDAP to Active Directory. SAML accomplishes the same goals, but for Modern Cloud Identity Providers.
SAML allows organizations to implement an SSO (Single Sign-On) policy and use their existing database credentials to authorize access to Wi-Fi and other applications. Using SAML and instituting an SSO policy will greatly improve the efficiency of your network and the overall user experience.
There are many benefits provided by an SSO policy that may not be considered at first glance.
Initially, SSO will greatly improve the network user experience. Instead of having to memorize several different passwords to access different applications, when a user is authenticated by the network, they are authorized for use of all applicable network applications. There are fewer passwords to remember, which makes for a much more efficient network experience.
For the network administrators, it simplifies the network setup because there are far fewer databases to manage. Without an SSO policy, each application would need a directory to confirm the identity of users and would create significantly more work in the setup and management processes.
Finally, the last perk to consider is the improvement to network safety, particularly against phishing attacks. If network users are properly educated about their network, they’ll know that any attempts to elicit credentials from them outside the initial sign-on is a phishing attack. No network application will request credentials because the SSO policy would have already confirmed their identity.
Outline for Configuring SAML for Wi-Fi Authentication
Of course, in order to experience these benefits, SAML must be properly configured for Wi-Fi authentication. In the following setup example, we’ll demonstrate the process using Google as our IDP and the JoinNow app from SecureW2 as our Wi-Fi onboarding software.
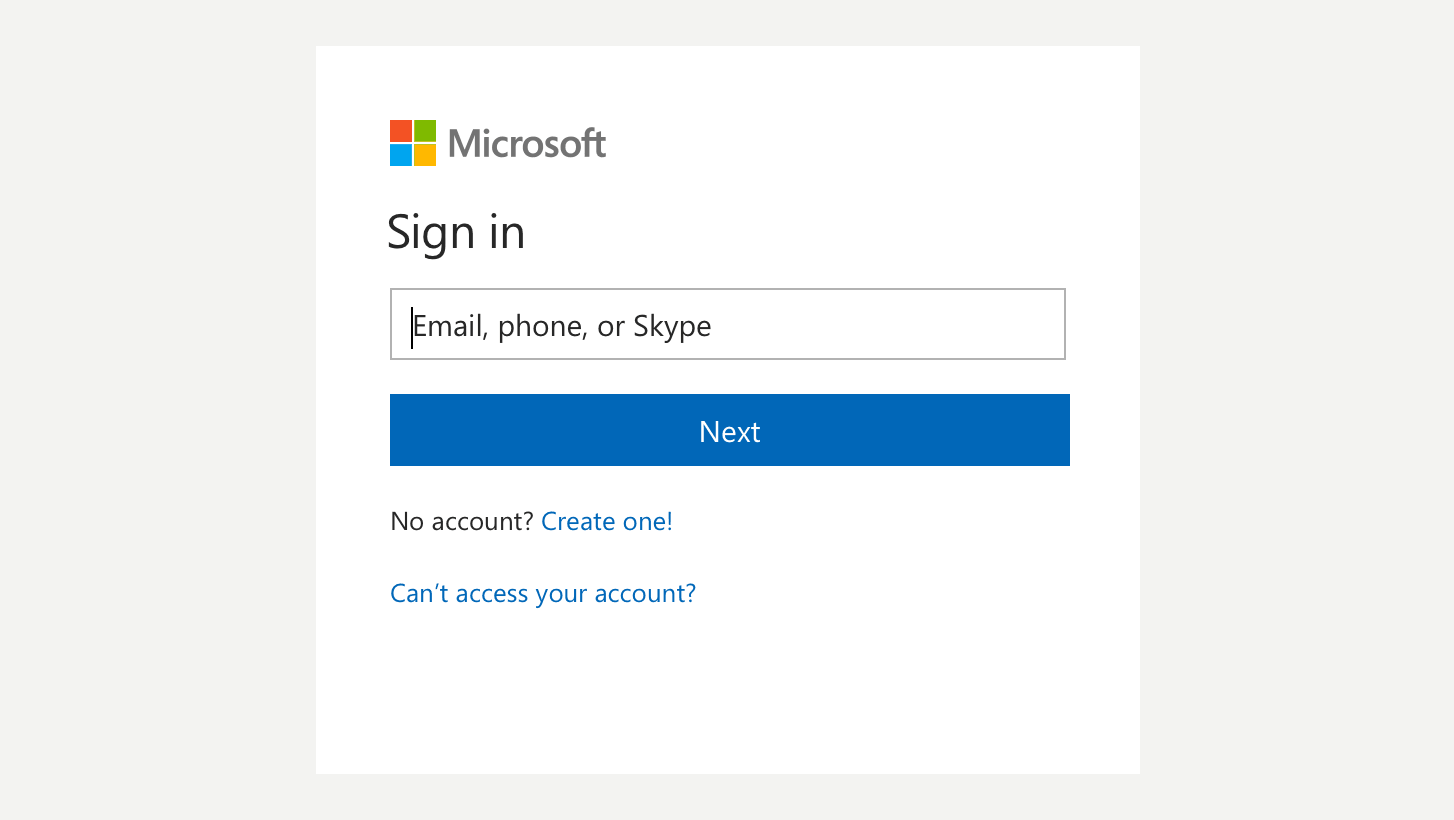
- A user enrolls via the JoinNow application. It requests information from the IDP to confirm the user’s identity.
- After a positive inquiry, a SAML token is translated into secure WPA2-Enterprise Wi-Fi access for the user.
- For the application to utilize the SAML token, there must be mutual trust created between the application and IDP.
- Exchange metadata between the application and the IDP to create mutual trust.
- Once the configuration is finalized, the SSO policy is completed and ready to authenticate network users.
When it comes to the user experience, network users value convenience and efficiency above all other factors. Using SAML to enable an SSO policy allows for streamlined access to network applications and limits the number of passwords per user. It also promotes many added security benefits, such as protecting against phishing and limiting the opportunities for a credential theft attack.
If your network is lacking in safety and hosts a poor user experience, implementing an SSO policy using SAML authentication may be the key to overall network improvement. SecureW2 offers affordable options for organizations of all shapes and sizes. Click here to inquire about pricing.