JoinNow Platform 8.3 is now available, featuring expanded integrations across a wide range of security platforms—enhancing real-time intelligence capabilities and delivering improvements to Intelligence Briefs.
This blog covers all the updates in detail, but below is a summary of the prominent ones:
- Tenable Integration: Use security insights from Tenable scanner to deter risky devices from entering your secure network.
- Zscaler integration: Use trust-based signals from Zscaler for lookups during certificate issuance and to inform network access decisions.
- Okta Identity Threat Protection (Okta ITP) Support: Include user risk signals as conditions for deciding on network authentication and certificate enrollment.
- Improved Intelligence Briefs with details on expired/expiring certificates
Let’s take a look at some of the major enhancements in more detail.
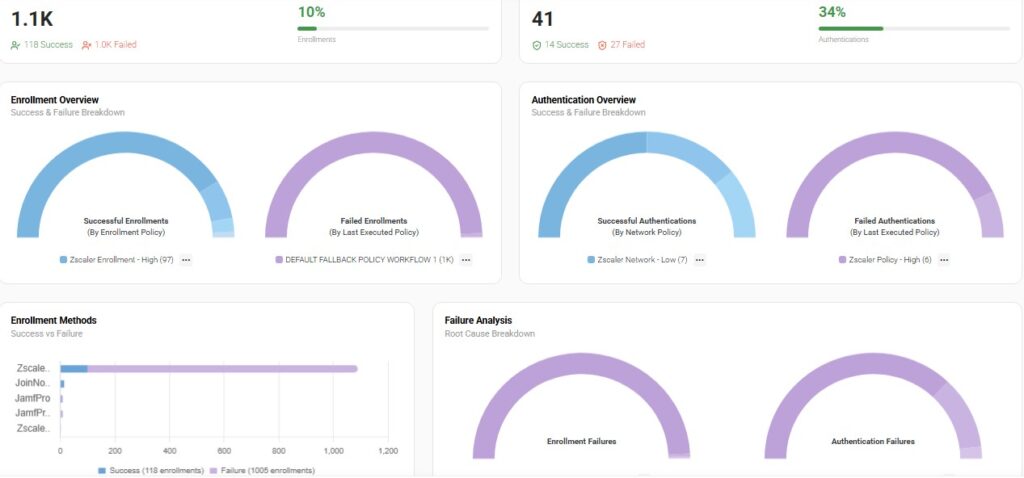
Improved Dashboard Layout
The main dashboard of the JoinNow Management Portal has been revamped with a modernized interface, making key metrics easier to access and review.
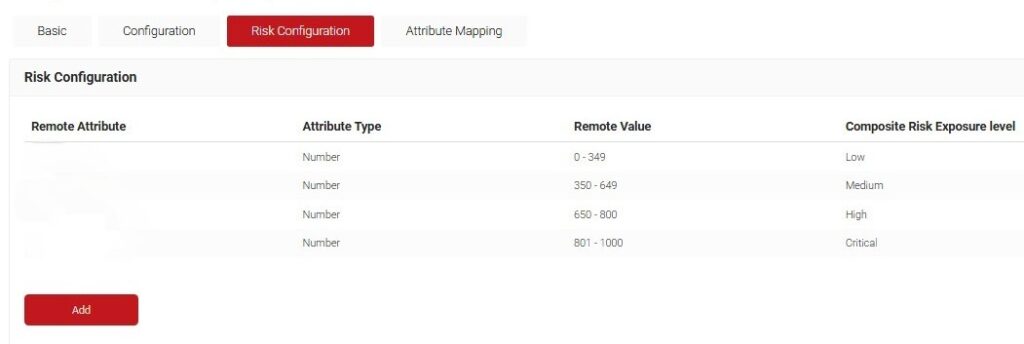
Vulnerability Scanner Integration: Tenable
Leverage Tenable’s vulnerability, misconfiguration, and exposure signals to automatically trigger tailored remediation actions for high-risk endpoints that request certificate enrollment or RADIUS authentication.
Use Security Platform menu to bring Tenable into the JoinNow Management portal and configure automated policies in Adaptive Defense.
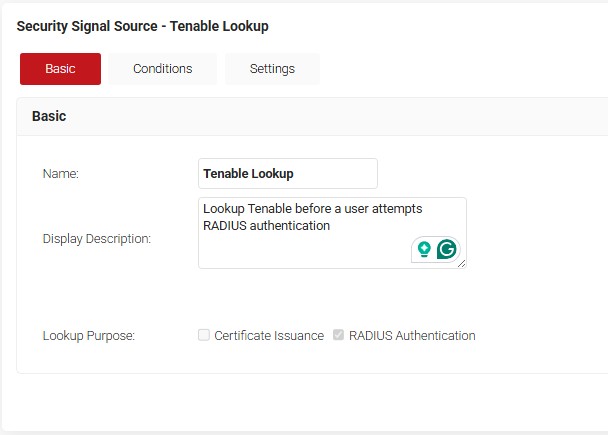
Adapt your access policies in real time when changes in risk are detected.
Use cases include, but are not limited to
- Automatically revoke active certificates issued to endpoints when Tenable identifies them as highly vulnerable.
- Creating separate or consolidated policy workflows for blocking a device from network access when it is active in Jamf and Tenable reports a high exposure score. Later unblocking when vice-versa is noted.
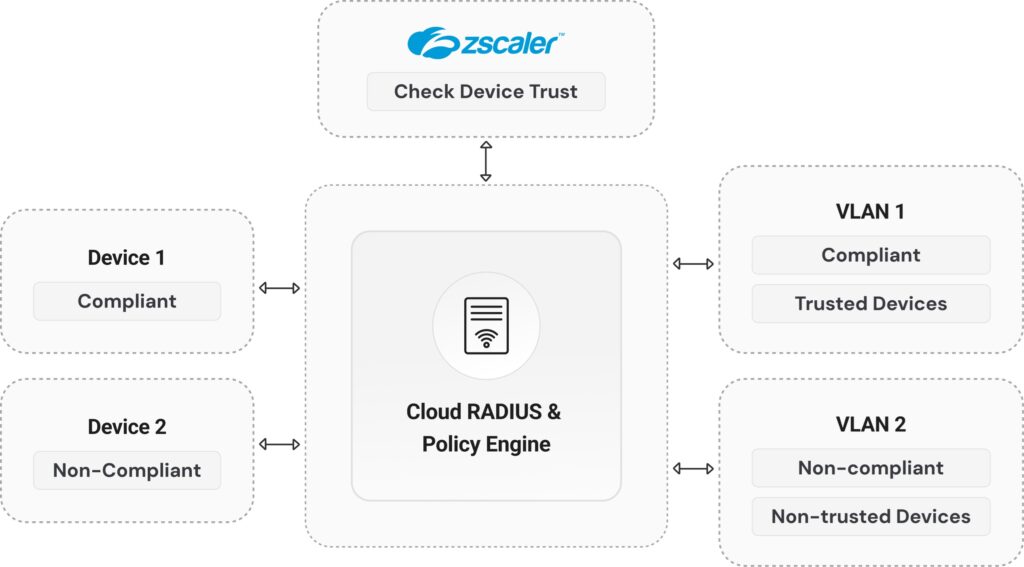
Zero Trust Platform Integration: Zscaler
SecureW2 now directly integrates with Zscaler to utilize its device trust signals, ensuring device compliance and security posture during certificate enrollment and RADIUS authentication.
Risk level of a device is calculated using its trust value in Zscaler and can be fed as a condition for certificate authentication policies.
You can also use Zscaler Trust to segment compliant devices from non-compliant ones and enforce stricter access controls for the latter.
Okta Identity Threat Protection (ITP) with Real-time Intelligence
SecureW2 customers can now ingest user risk scores from Okta ITP to assess risk prior to issuing certificates and granting RADIUS authentication, enabling them to proactively mitigate potential network threats.
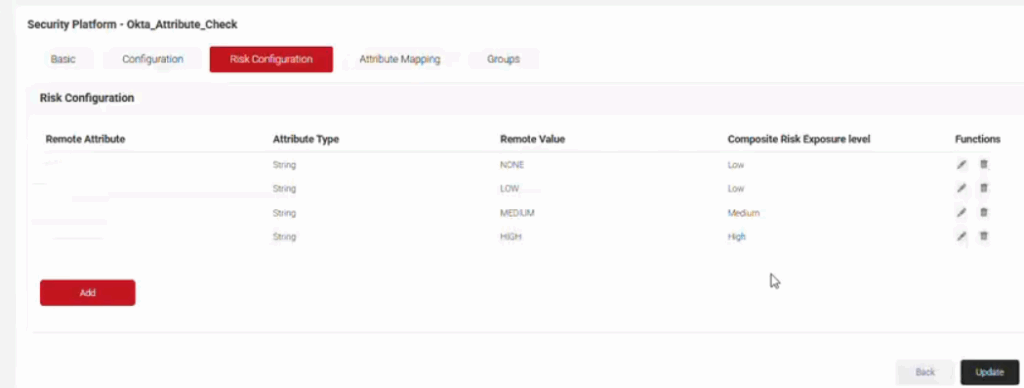
Furthermore, the derived risk values can be used to define adaptive access controls for certificate authentication policies. You can revoke/suspend certificates and block/unblock network access.
New Intelligence Briefs
The Intelligence Briefs dashboard now provides a quick summary of the count of certificates expiring within the next 90 days and those that have already expired (within 90 days).

What’s new?
- The new dashboard has a count of the certificates at the Intermediate CA level.
- Displays the count in categories as 0–15, 16–30, 31–60, and 61–90 days.
- Notification emails on the expiry can be sent to Administrators/Business owners as well.
Continued User Experience Improvements
In addition to these core features, JoinNow Platform 8.3 includes some updates to improve user experience and platform organization:
- Expiring and expired certificate reports in Data & Monitoring → Reports can now display the duration of expiry.
- Enhanced events can now be filtered based on event flags, such as success or failure.
This concludes the key updates in our latest release. We believe JoinNow Version 8.3 solidifies SecureW2’s leadership as a modern Passwordless Platform that continuously enforces user and device trust across your environment.
To explore how these new features can modernize your authentication and reduce your attack surface, contact us today!