Overview
The Access Server external public key infrastructure (PKI) feature integrates Access Server with third-party tools for X509 PKI management instead of using the built-in certificate management capabilities.
When configured for external PKI usage, Access Server doesn’t manage client certificates directly; instead, the customer’s third-party PKI software generates and distributes client certificate/key pairs to client machines and a server certificate/key pair to the OpenVPN server.
This tutorial shows you how to set up external PKI using SecureW2.
At a high level, these are the steps for your configuration:
- Modify as.conf to set Access Server in external PKI mode.
- Create the server and intermediate using SecureW2.
- Create certificate templates for the server and clients via SecureW2.
- Generate the server certificate and key via SecureW2.
- Generate the client certificate and key via SecureW2.
- Create the TLS_auth key.
- Generate Diffie-Hellman parameters.
- Import the necessary certificate and key files to the Access Server.
- Provide certificate/key pairs in a P12/PFX file to the VPN client.
- Generate and download a server-locked profile for the client.
Prerequisites
- An installed Access Server.
- A SecureW2 account and access to the Management Portal.
- Console access and the ability to get root access.
- An OpenVPN client that supports the macOS Keychain and Windows certificate store.
Step 1: Set Access Server to external PKI mode
- Connect to the Access Server console and get root privileges.
- Edit as.conf for external PKI usage:
nano /usr/local/openvpn_as/etc/as.conf
- Comment out certs_db:
# certificates database # certs_db=sqlite:///~/db/certs.db
- Save and exit the file — ctrl+x, y, then enter.
- Access Server no longer uses the certificate database. Instead, an external system must handle this.
Step 2: Create a Server CA
To add a Root CA, follow these next steps:
- Log in to the JoinNow Management Portal.
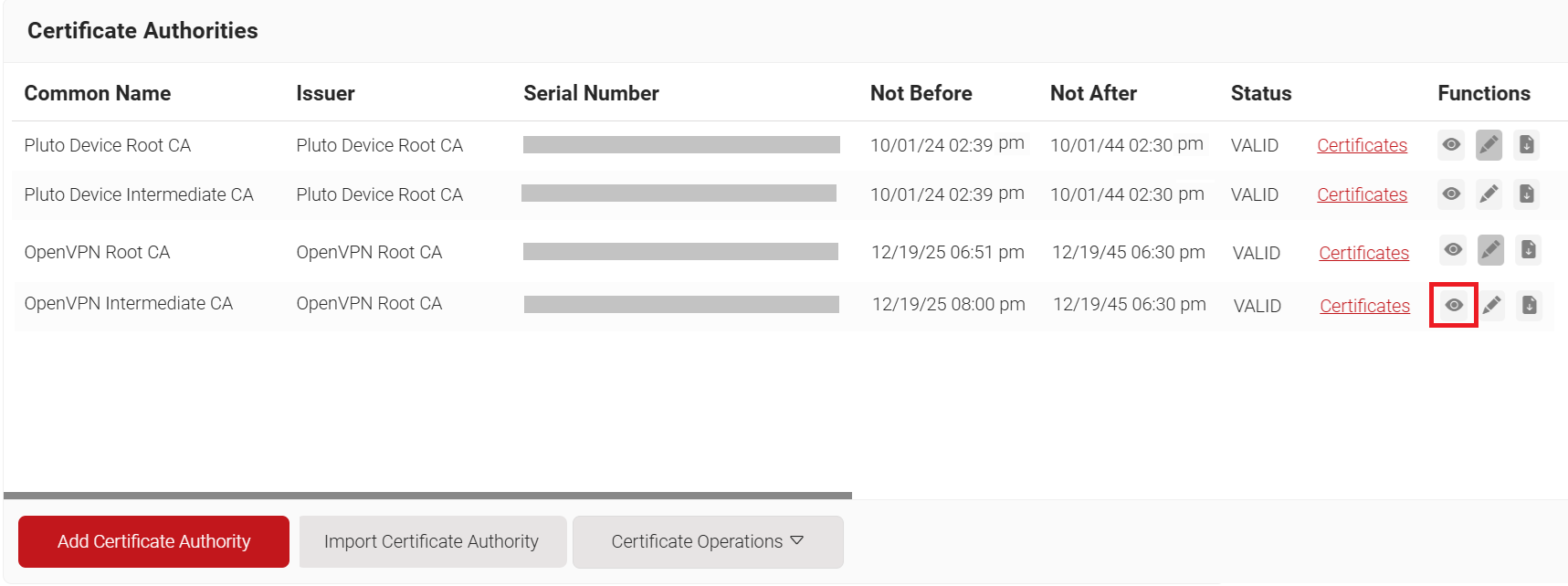
- Navigate to Dynamic PKI > Certificate Authorities.
- Click Add Certificate Authority.
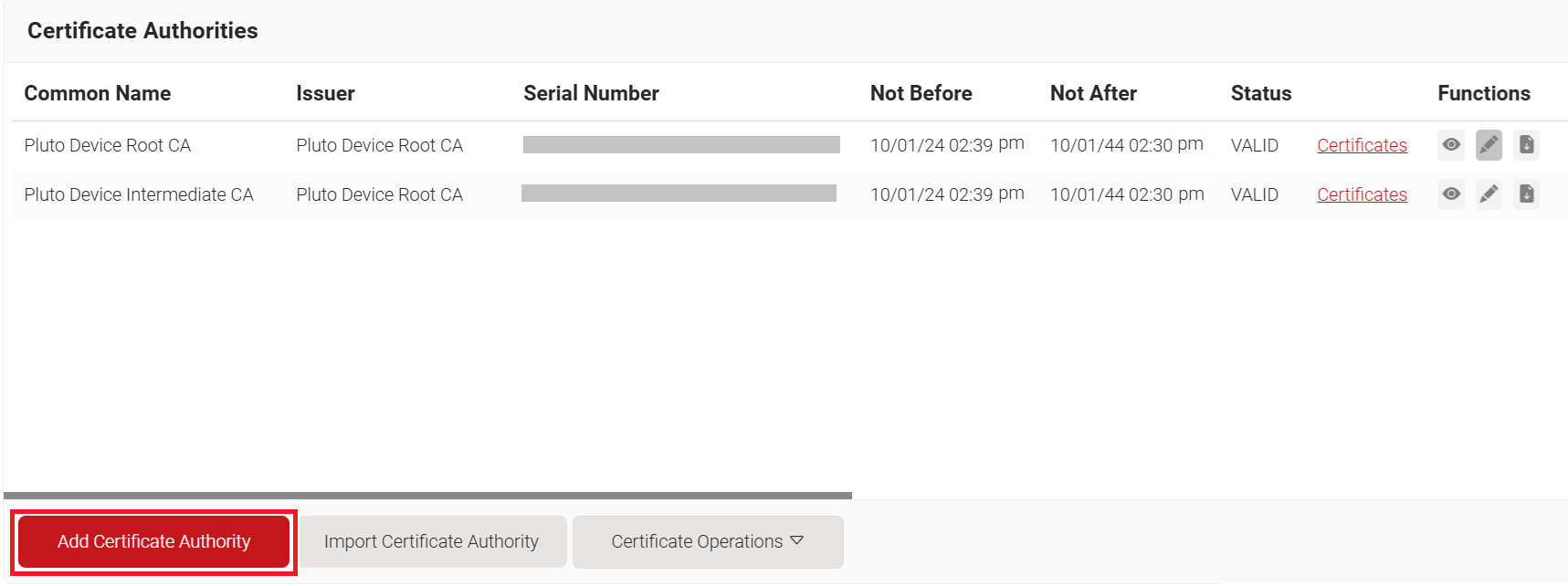
- In the Basic section, from the Generate CA For drop-down list, select the Device and User Authentication option to authenticate devices and users.
- From the Type drop-down list, select Root CA.
- In the Common Name field, enter the common name of the root CA (e.g., “OpenVPN Root CA”).
- From the Key Size drop-down list, select 2048 for the CA certificate key pair.
- From the Signature Algorithm drop-down list, select the signature algorithm for the certificate signing request. The option available is SHA-256.
- In the Validity Period (in years) field, enter the validity period of the CA certificate.
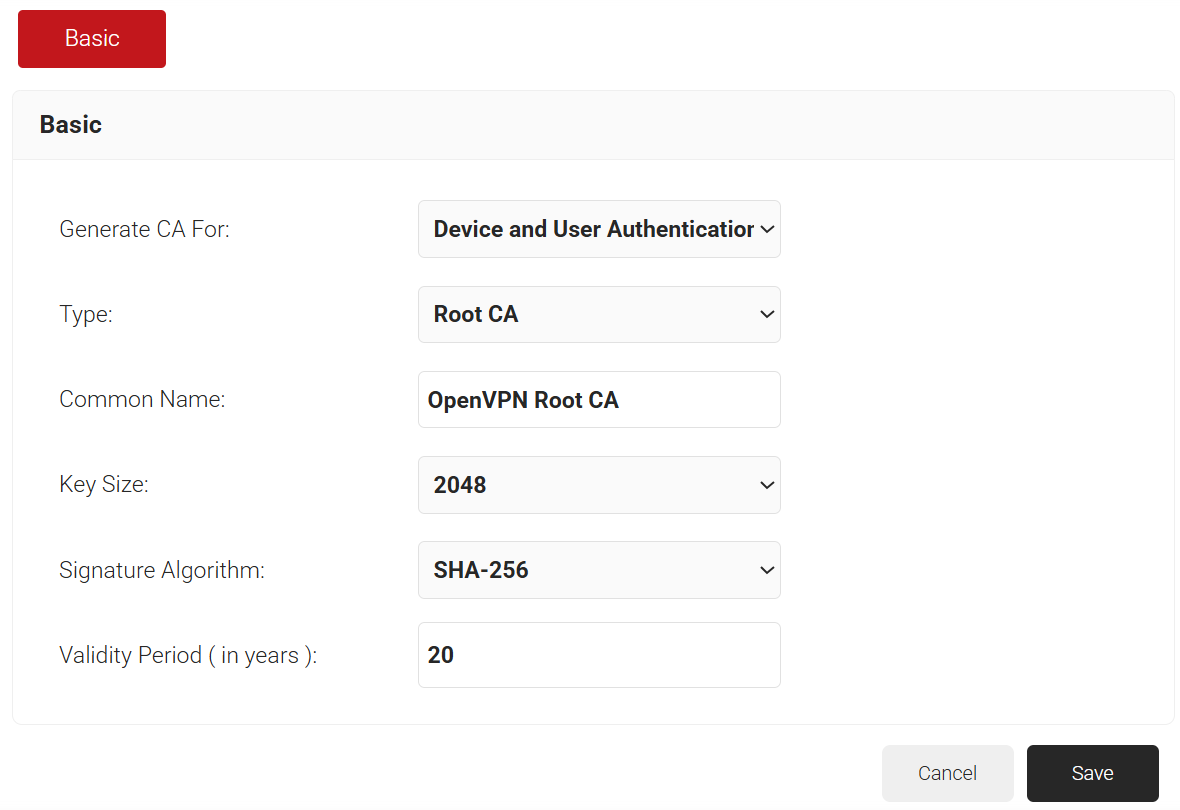
- Click Save.
Step 3: Create an Intermediate CA
SecureW2 recommends the use of an Intermediate CA as a best practice for easy identification and management of your CAs.
To create a new intermediate CA:
- Navigate to Dynamic PKI > Certificate Authorities.
- Click Add Certificate Authority.
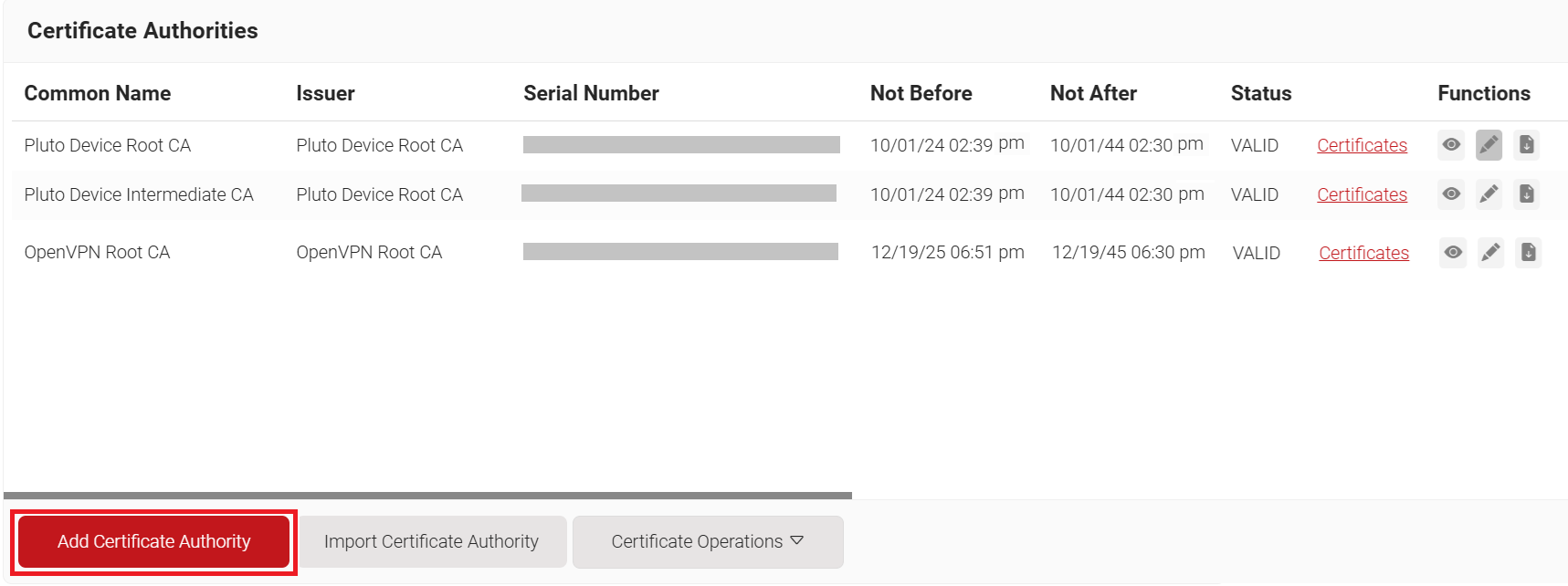
- In the Basic section, from the Generate CA For drop-down list, select the Device and User Authentication option to authenticate devices and users.
- From the Type drop-down list, select Intermediate CA.
- From the Certificate Authority drop-down list, select either an internal or external CA.
- In the Common Name field, enter the Common Name for the intermediate CA (e.g., “OpenVPN Intermediate CA”).
- From the Key Size drop-down list, select 2048 for the CA certificate key pair.
- From the Signature Algorithm drop-down list, select the signature algorithm for the certificate signing request. The option available is SHA-256.
- In the Validity Period (in years) field, enter the validity period for the Intermediate CA in terms of the number of years.
- In the Notifications section:
- From the Expiry Notification Frequency (in days) drop-down list, select the frequency interval for which a certificate expiration notification should be sent to users.
- Select the Notify user on successful Enrollment checkbox to notify users after a successful enrollment.
- In the Revocation section:
- In the Revoke Certificate if unused for field, select the number of days after which an unused certificate can be revoked.
- Since last usage – Select this checkbox to revoke the certificate after a specified number of days if it remains unused.
- Since certificate issuance – Select this checkbox to revoke the certificate after a specified number of days after it is issued.
- From the Reason Code drop-down list, select any one of the following reasons for which the certificate is revoked.
- Certificate Hold
- AA Compromise
- Privilege Withdrawn
- Unspecified
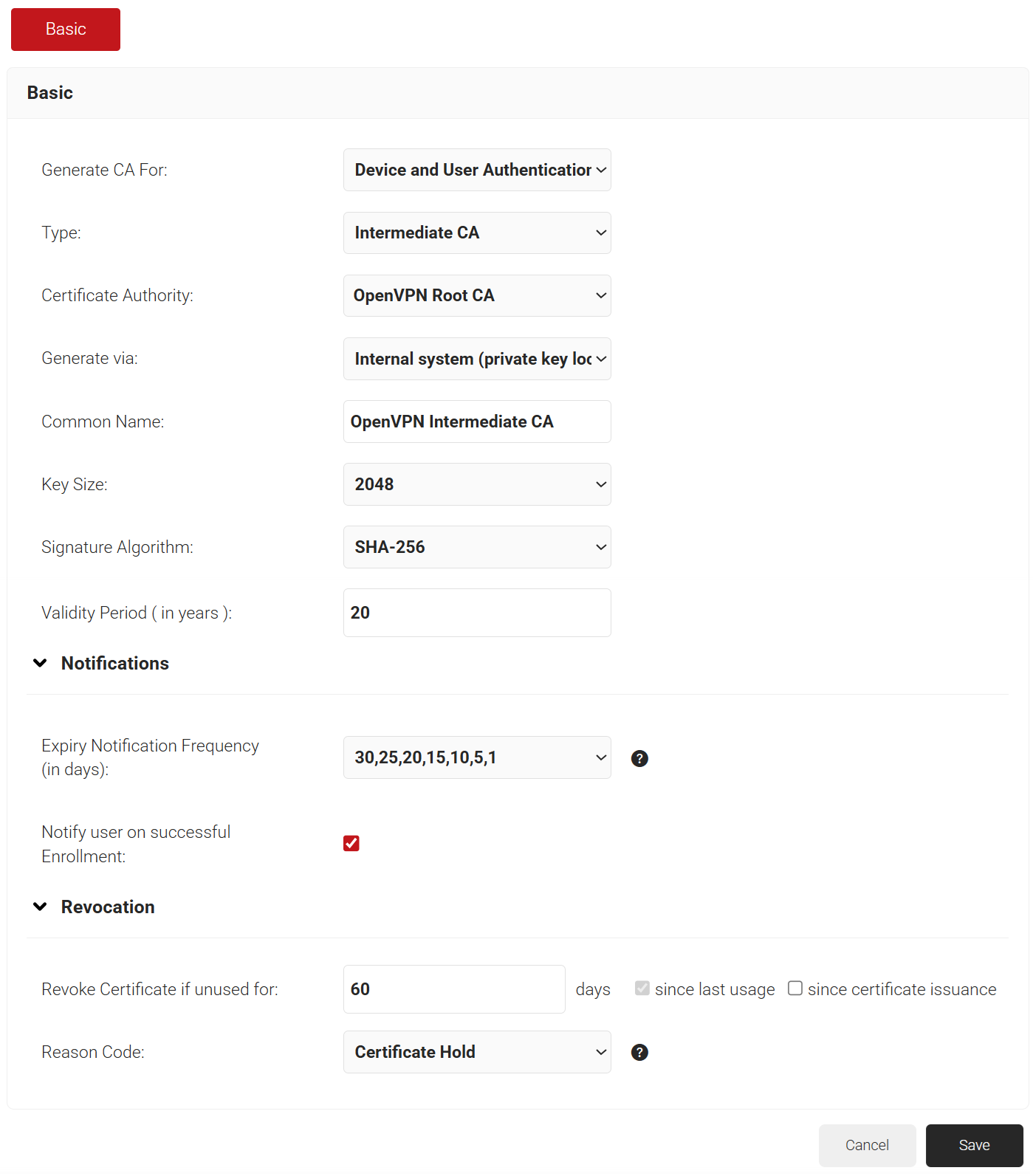
- In the Revoke Certificate if unused for field, select the number of days after which an unused certificate can be revoked.
- Click Save.
Step 4: Create a Server Template
A certificate template defines how information is encoded in a certificate issued by the Certificate Authority. It includes a list of certificate attributes and specifies how information must be encoded in each attribute value.
To create a server template, perform the following steps:
- Navigate to Dynamic PKI > Certificate Authorities.
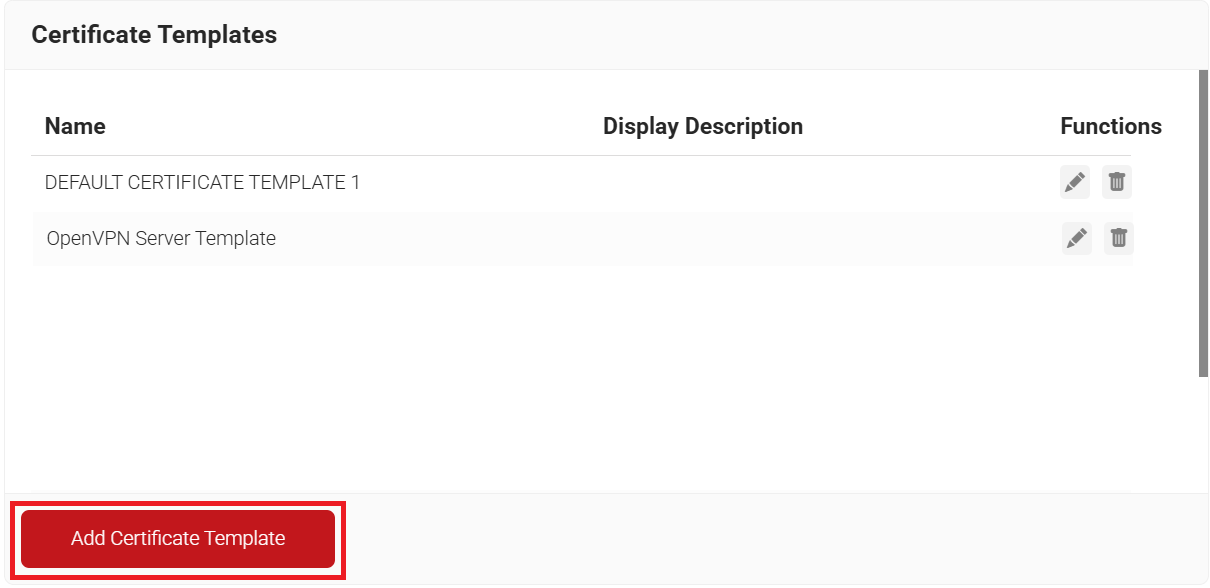
- Scroll to the Certificate Templates section and click Add Certificate Template.
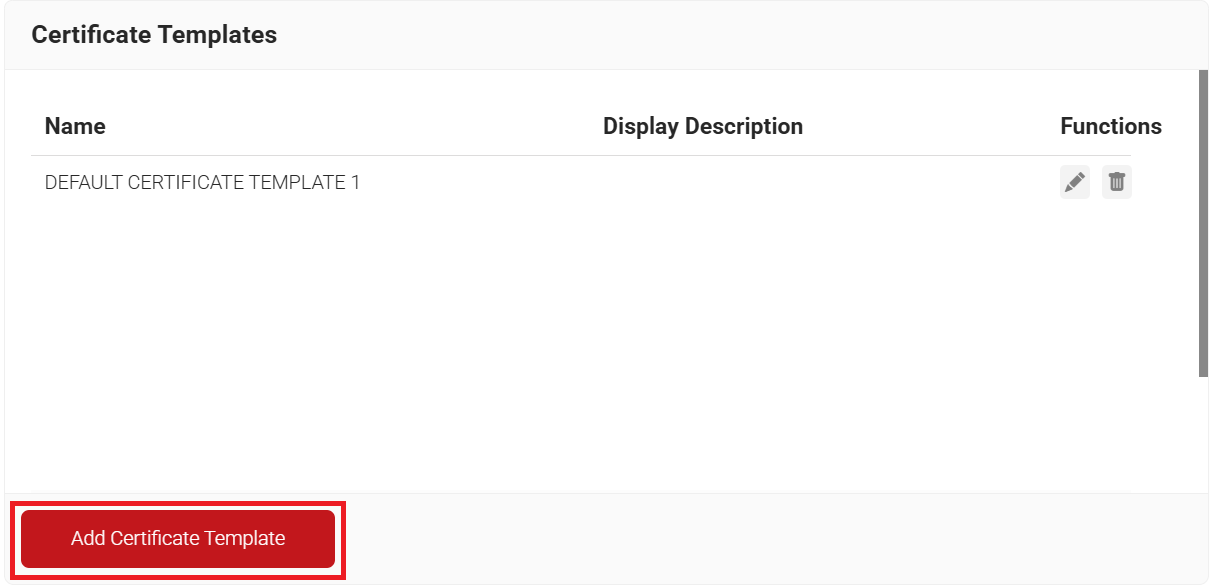
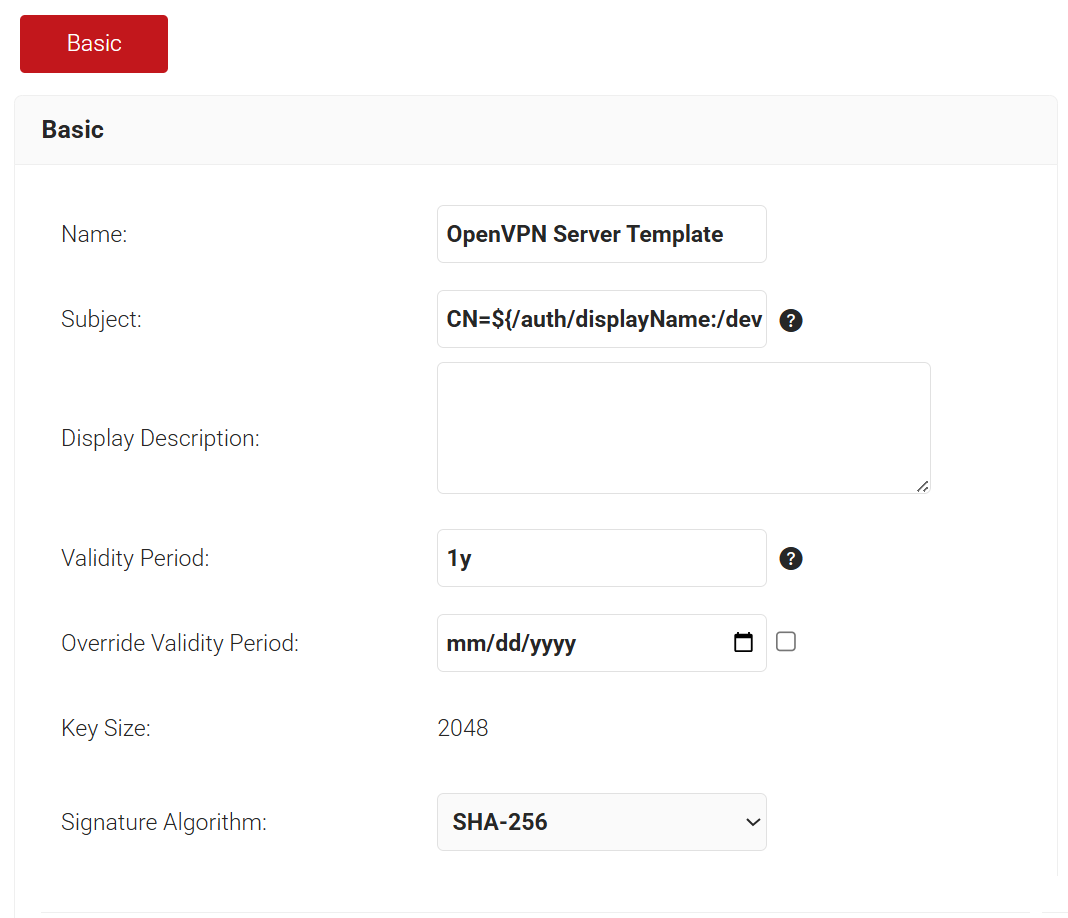
- In the Basic section, enter the name of the server template in the Name field (e.g., “OpenVPN Server Template”).
- In the Validity Period field, enter the validity period of the server template in d m y format (e.g., “0d 0m 1y” represents one year).
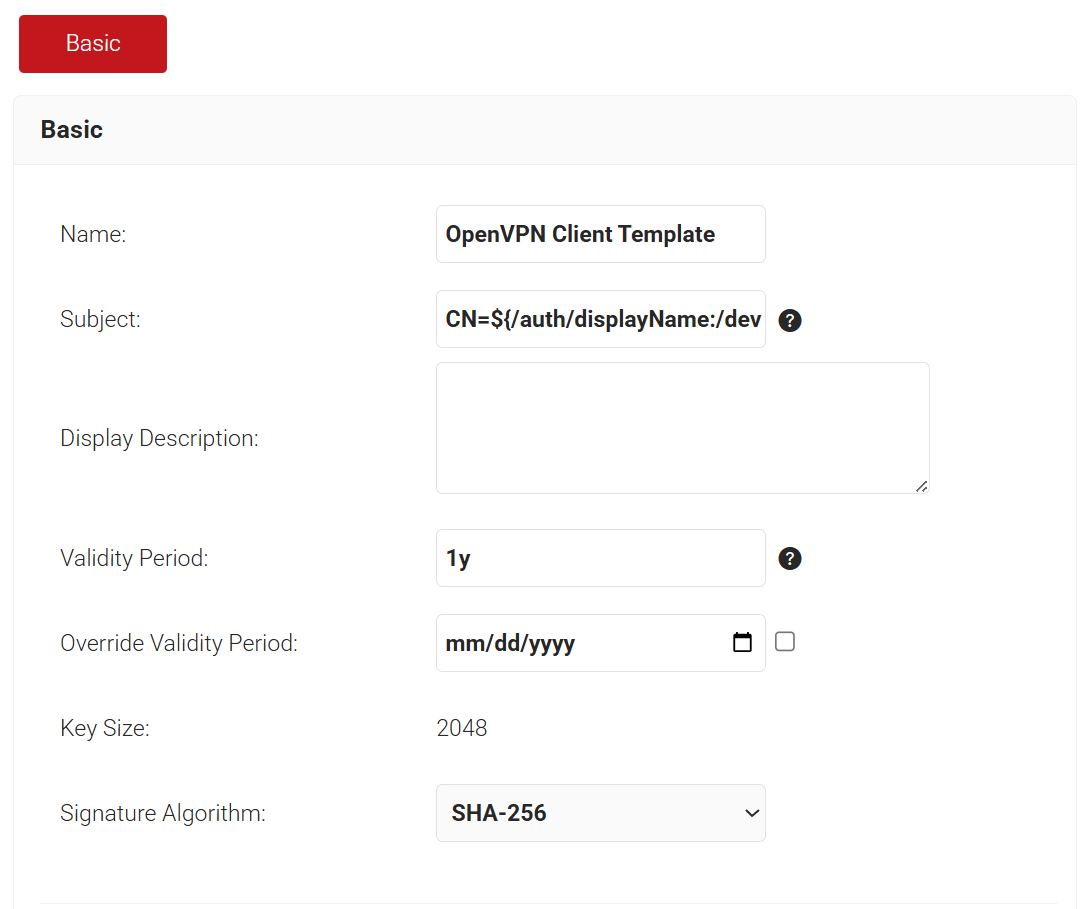
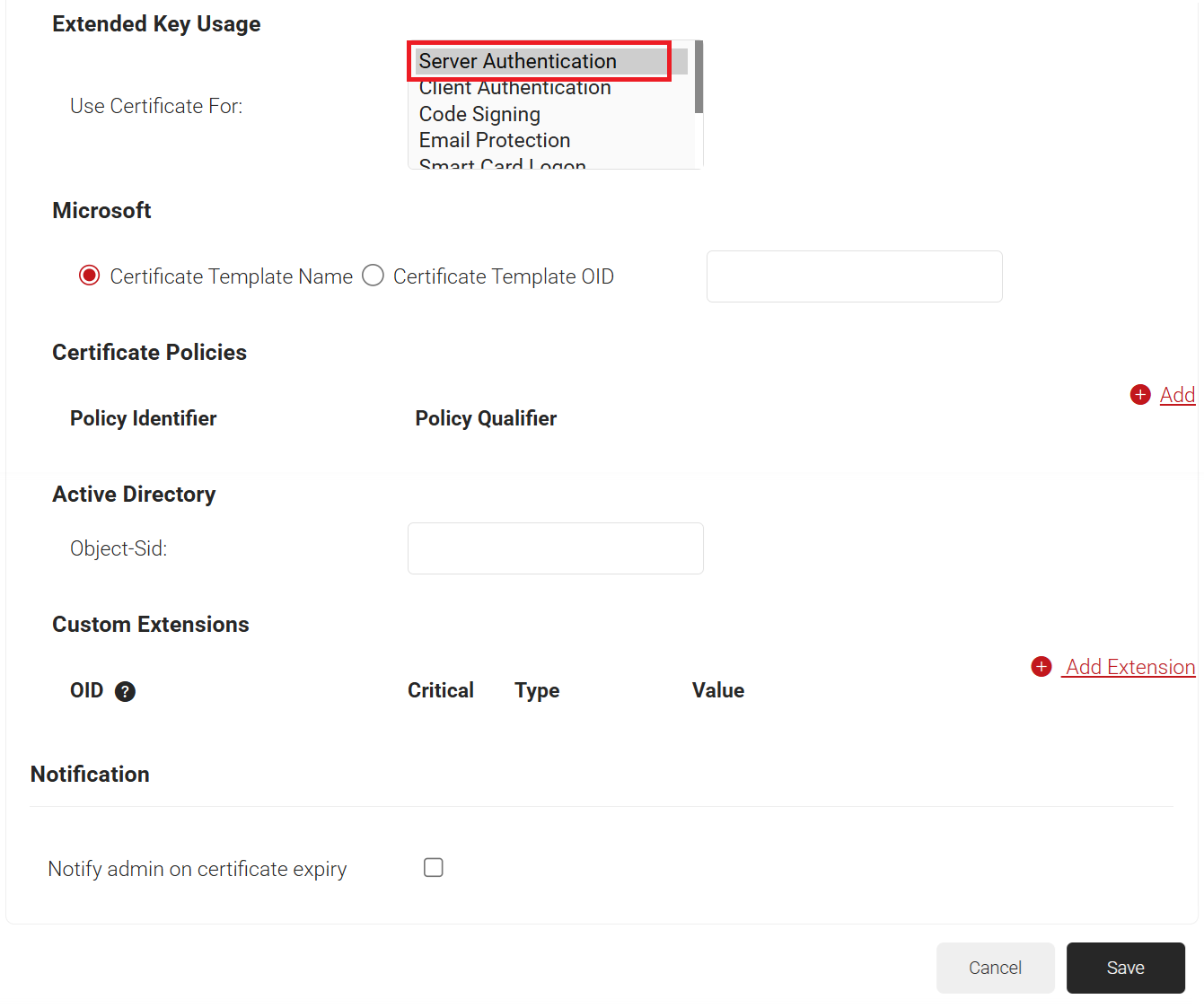
- In the Extended Key Usage section, from the Use Certificate For list, select Server Authentication.
- Click Save.
Step 5: Create a Client Template
To create a client template, perform the following steps:
- Navigate to Dynamic PKI > Certificate Authorities.
- Scroll to the Certificate Templates section and click Add Certificate Template.
- In the Basic section, enter the name of the client template in the Name field (e.g., “OpenVPN Client Template”).
- In the Validity Period field, enter the validity period of the client template in d m y format (e.g., “0d 0m 1y” represents one year).
- (Optional, for deployments using auto-login profiles.) Under Certificate Extensions, in SAN > Other Name, replace the existing value with autologinrole.
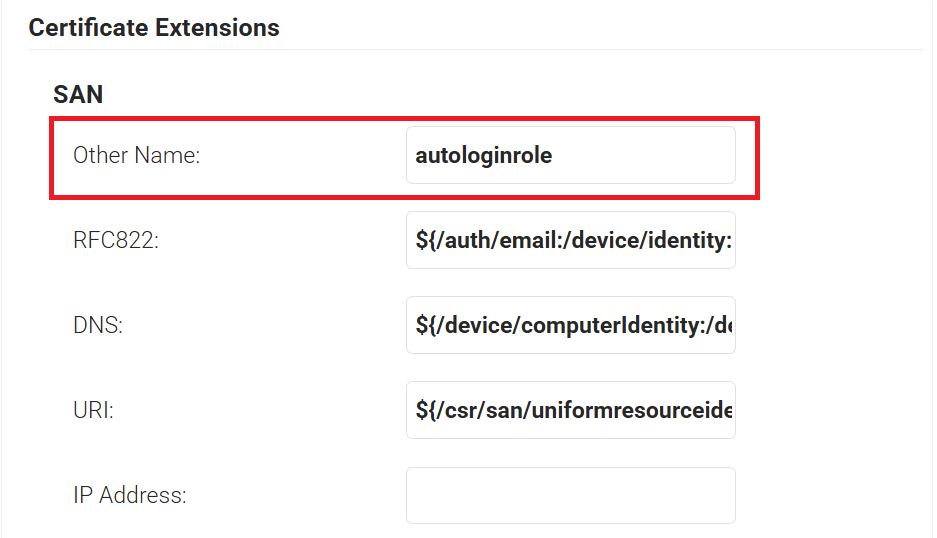
- In the Extended Key Usage section, from the Use Certificate For list, select Client Authentication.
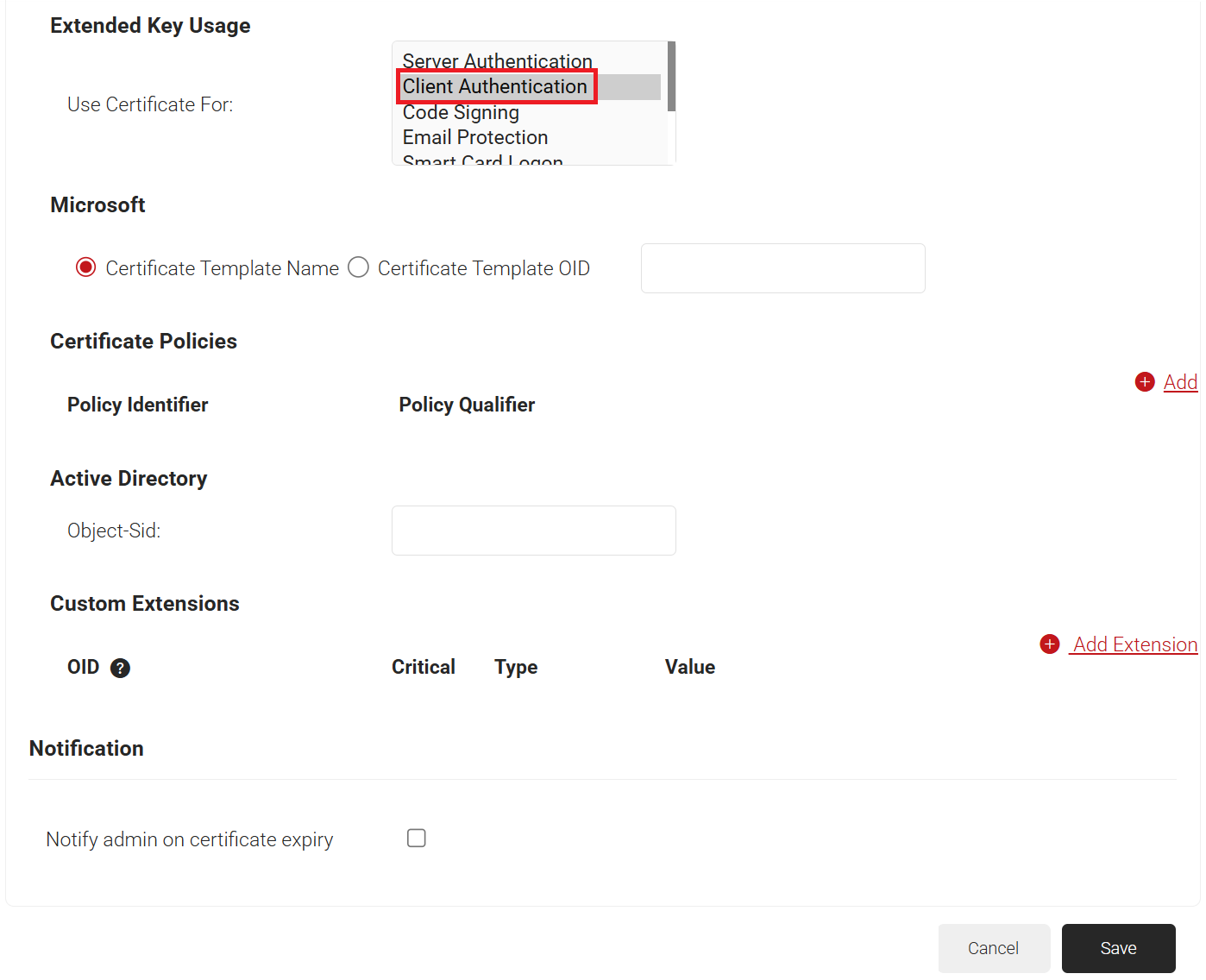
- Click Save.
Step 6: Create a Server Certificate and Key
To create a server certificate and key, perform the following steps:
- Navigate to Dynamic PKI > Create Certificate.
- In the Device Info section, from the Operating System drop-down list, select Linux.
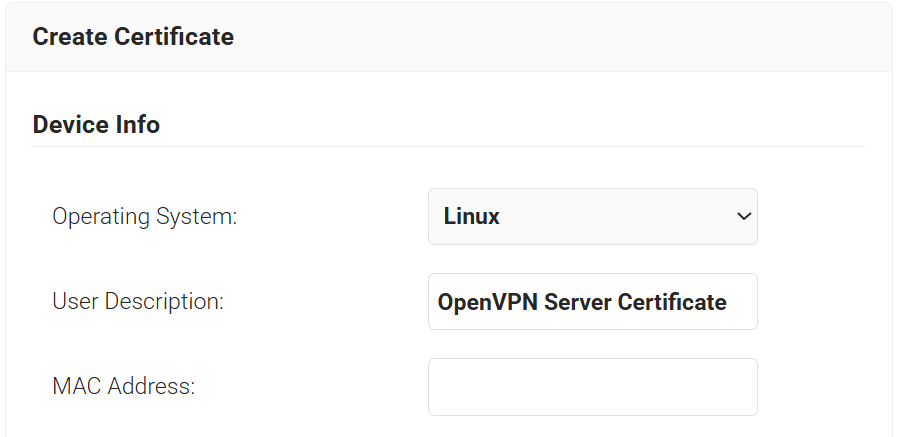
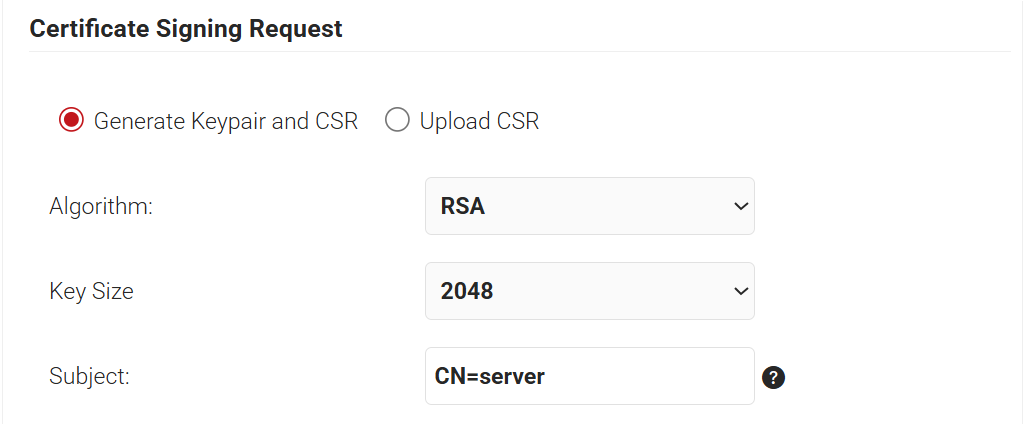
- In the Certificate Signing Request section:
- Select Generate Keypair and CSR.
- In the Subject field, type the common name of the Server Certificate (e.g., “CN=server”).
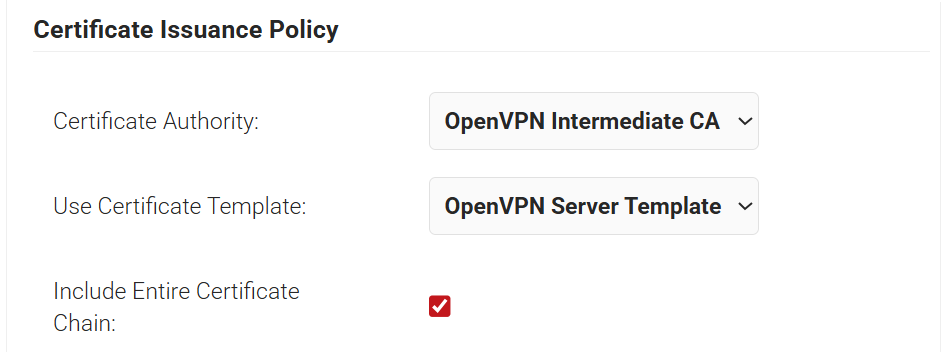
- In the Certificate Issuance Policy section:
- From the Certificate Authority drop-down list, select the Intermediate CA created in Step 3.
- From the Use Certificate Template drop-down list, select the Server Template created in Step 4.
- Select the Include Entire Certificate Chain checkbox.
- In the Distribution section:
- In the Format field, select PEM.
- In the Receive via field, select Download.
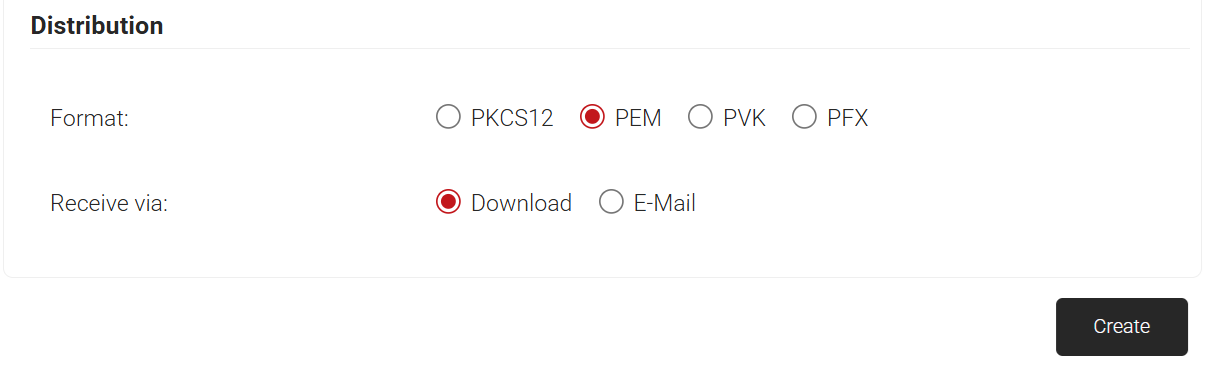
- Click Create.
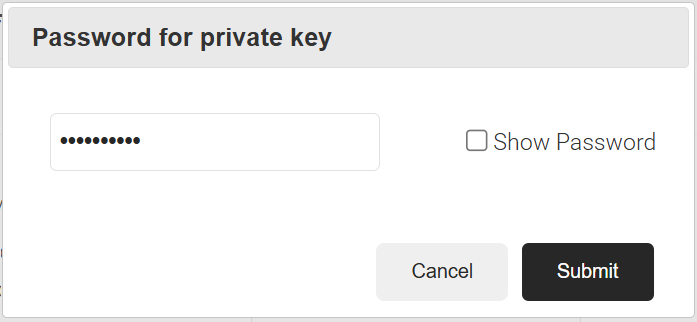
- You’ll be prompted to create a password for the server’s private key.
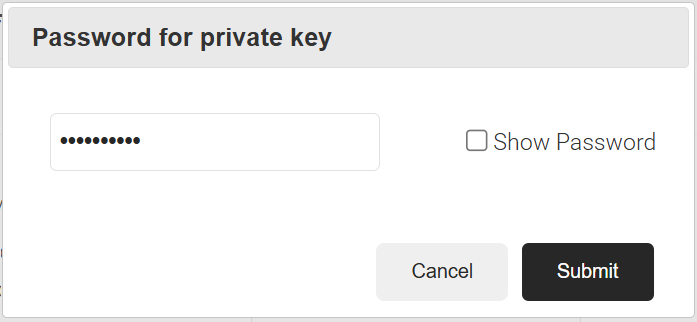
- You’ll be prompted to create a password for the server’s private key.
- A ZIP file downloads with the following files:
- Server Certificate (server.crt)
- Server Key (server.key)
- CA Bundle (cacert.crt)
Step 7: Create a Client Certificate and Key
To create a client certificate and key, perform the following steps:
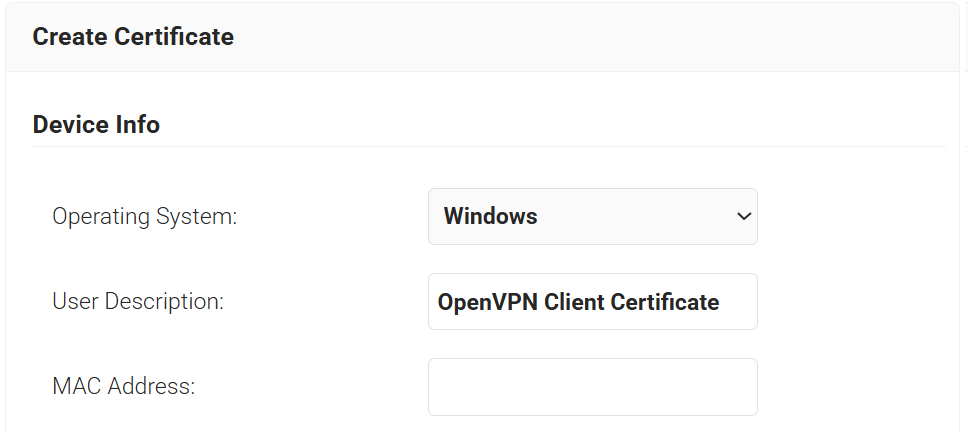
- Navigate to Dynamic PKI > Create Certificate.
- In the Device Info section, from the Operating System drop-down list, select your VPN user’s operating system (e.g., Windows or macOS).
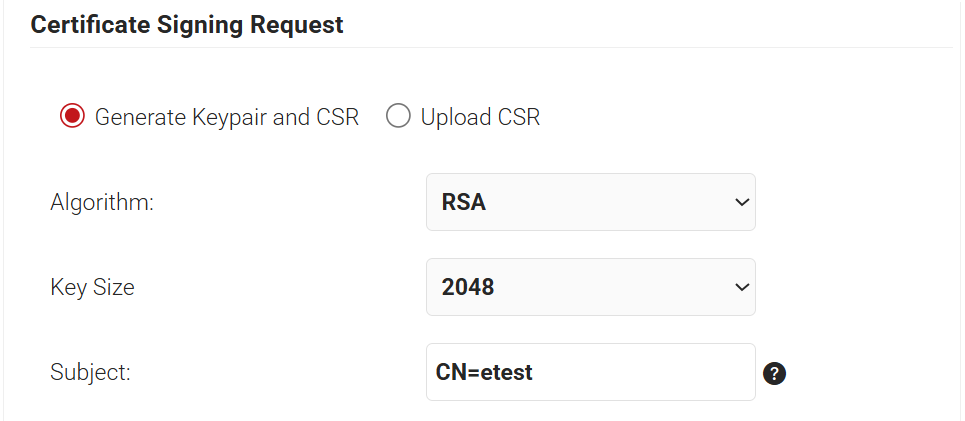
- In the Certificate Signing Request section:
- Select Generate Keypair and CSR.
- In the Subject field, type the client certificate’s common name of the Client Certificate (e.g., “CN=etest”).
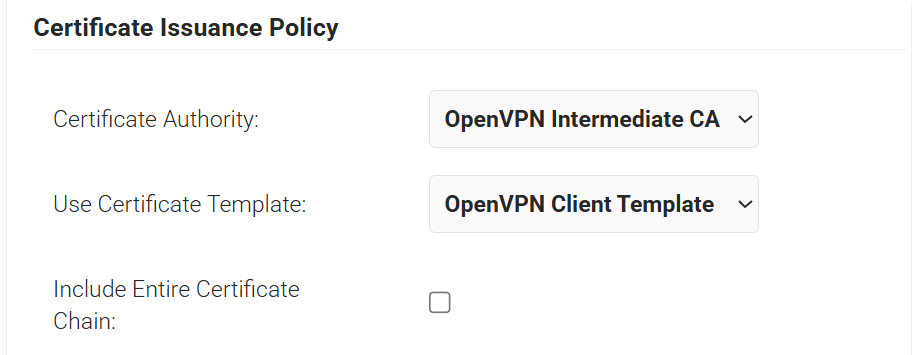
- In the Certificate Issuance Policy section:
- From the Certificate Authority drop-down list, select the Intermediate CA created in Step 3.
- From the Use Certificate Template drop-down list, select the Client Template created in Step 5.
- In the Distribution section:
- In the Format field, select PCKS12.
- In the Receive via field, select Download.
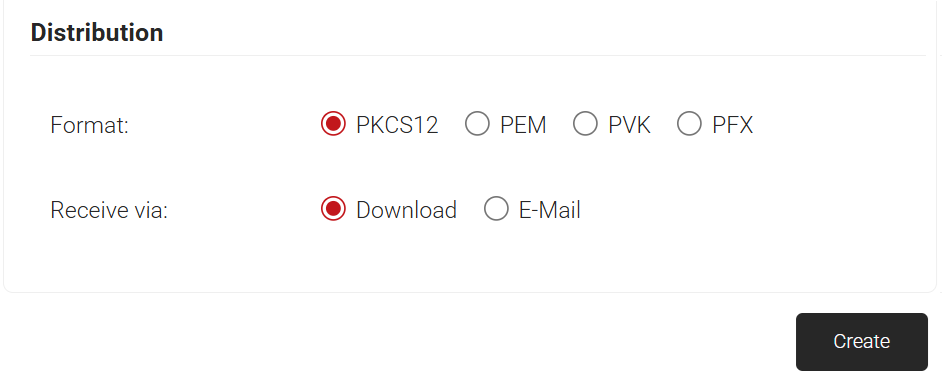
- Click Create.
- You’ll be prompted to create a password for the client’s private key.
- You’ll be prompted to create a password for the client’s private key.
- The client P12 file (“etest.p12”) outputs.
Step 8: Configure Access Server Files
- Connect to the Access Server console and get root privileges.
- Create a directory:
mkdir epki && cd epki
- Place the CA bundle, server certificate, and key generated from SecureW2 via WinSCP or SCP in this new “epki” directory.
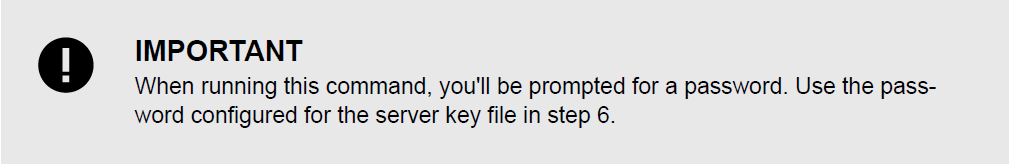
- Remove the password from the server key:
openssl rsa -in server.key -out newserver.key
- Create a tls_auth key for the OpenVPN server:
/usr/local/openvpn_as/scripts/certool --tls_auth
- Generate Diffie Hellman parameters for the OpenVPN server:
openssl dhparam -out dh.pem 2048
- Generate your auth token and add the generated file:
/usr/local/openvpn_as/scripts/certool --auth_token
- Configure X509 explicit/extended key usage based on RFC3280 TLS rules:
/usr/local/openvpn_as/scripts/sacli --key "external_pki.remote_cert_usage" --value
eku ConfigPut - Configure the use of the X509 “role” attribute for the declaration of auto-login permission:
/usr/local/openvpn_as/scripts/sacli --key "external_pki.autologin_x509_spec" --value
"subjectAltName,,autologinrole" ConfigPut - Generate the tls-crypt-v2 key:
/usr/local/openvpn_as/scripts/certool --tls_crypt2_server
- Load the newly generated files into the Access Server config database:
/usr/local/openvpn_as/scripts/sacli --key "external_pki.ta_key" --value_file ta.key ConfigPut
/usr/local/openvpn_as/scripts/sacli --key "external_pki.ca_crt" --value_file cacert.crt ConfigPut
/usr/local/openvpn_as/scripts/sacli --key "external_pki.server_crt" --value_file server.crt ConfigPut
/usr/local/openvpn_as/scripts/sacli --key "external_pki.server_key" --value_file newserver.key ConfigPut
/usr/local/openvpn_as/scripts/sacli --key "external_pki.dh_pem" --value_file dh.pem ConfigPut
/usr/local/openvpn_as/scripts/sacli --key "external_pki.auth_token_key" --value_file auth_token.key ConfigPut
/usr/local/openvpn_as/scripts/sacli --key "external_pki.tls_cryptv2_server" --value_file tls_crypt2.key ConfigPut - Start Access Server:
systemctl restart openvpnas
Step 9: Configure a Test Client
To test our example, we generate a test client, etest.
- Sign in to the Admin Web UI.
- Click Users.
- Click Add New User.
- Click User Management > User Permissions.
- Create the new user, etest, and click Save.
- (Optional, for environments using auto-login profiles.) Under Permissions, set Allow Auto-login to Enabled, then Save.
- Click Reset Password.
- Enter a password and click Reset.
- Click Restart.
- Finally, generate a server-locked profile. The profile will be stored in etest.ovpn:
sacli GetGeneric >etest.ovpn
For generating an auto-login profile:
sacli --user etest GetAutologin >etest.ovpn
- Copy these two files to the client machine:
- Client P12 file (etest.p12)
- Client profile (etest.ovpn)
Step 10: Import the client profile and the client P12 file into OpenVPN Connect v3
- Launch OpenVPN Connect v3.
- Import the connection profile, etest.ovpn.
- Click Menu > Certificate & Tokens.
- Under PKCS#12, click the Add icon.
- Select your client P12 file (etest.p12).
- Enter the password for this file that you previously configured and click OK.
- Go back to the Home.
- Click Menu > My Profiles.
- Click or tap the Edit icon for the profile.
- Under Certificate and Key, click or tap Assign.
- Select the hardware token and click Confirm.
- Save the changes.
- Click or tap to connect.
Simplified ePKI client configuration (Access Server 2.14.2 and later)
With the release of Access Server 2.14.2, we’ve made configuring client connection profiles for ePKI easier. Previously, creating these profiles required using the command line, as noted in the tutorial.
However, in version 2.14.2 and later, you can now create and manage ePKI client connection profiles directly from Access Server’s Client Web UI.
There are two types of ePKI profiles available:
- Generic ePKI profile:
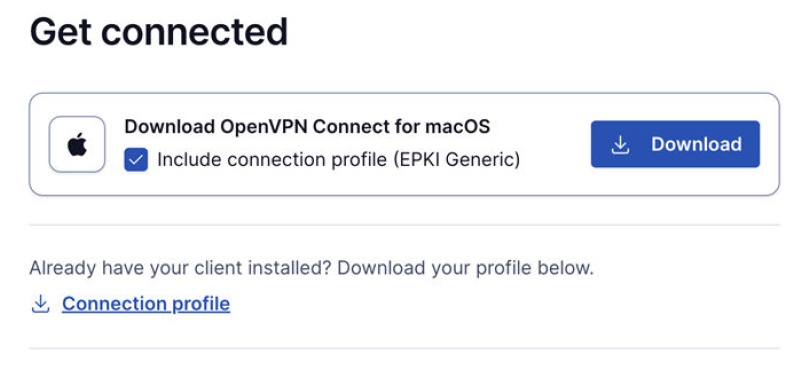
- This profile requires the user to authenticate with a password when connecting.
- Ideal for environments where a password-based security layer is needed in addition to certificate-based authentication.
- Auto-login ePKI profile:
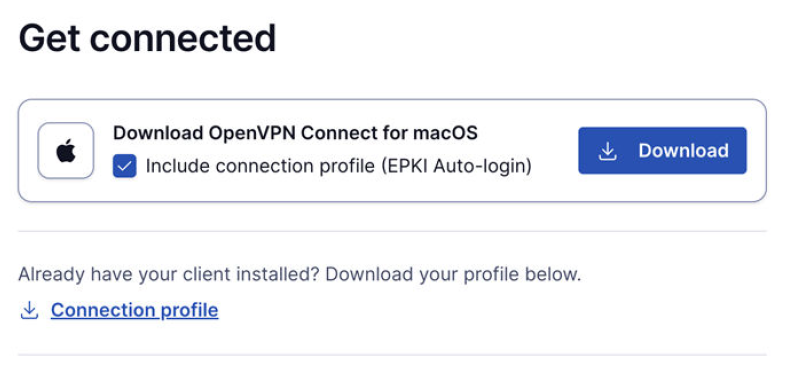
- This profile automatically uses the certificate for authentication without requiring a password.
- Suitable for unattended devices or systems where automatic, certificate-based login is needed.
In addition, the Import Profile from URL functionality in OpenVPN Connect allows users to import these connection profiles directly, making the configuration process faster and more seamless.
This update simplifies the ePKI setup, providing more flexibility and reducing the reliance on the command line.
Certificate Revocation Lists
A Certificate Revocation List (CRL) is a digitally-signed list maintained by a Certificate Authority (CA). It contains the serial numbers of certificates revoked before their scheduled expiration date. CRLs are a critical security mechanism in any PKI deployment, allowing administrators to immediately invalidate compromised or untrusted certificates.
In Access Server, CRLs ensure that VPN clients using revoked certificates can’t authenticate. Even certificates that are otherwise valid can be immediately blocked when security circumstances change.
Configuration and usage
- A CRL allows administrators to deny access to specific client certificate serial numbers.
- If a client attempts to connect using a certificate listed in the CRL, access is denied.
- Any client already connected whose certificate appears in the CRL at the time it’s loaded is immediately disconnected.
- The CRL field is specified via the vpn.server.crl key and initially loaded using:
sacli start
- Once loaded, the CRL file may be updated at any time. The Access Server automatically reloads it within a few seconds.
- Reload timing is controlled by the vpn.server.crl_resample key (integer, in seconds, default = 10).
- The CRL file must be in PEM format.
Add a CRL to Access Server
Follow these steps to retrieve and enable a CRL in ePKI mode.
1. Obtain the CRL from SecureW2
- Log in to the JoinNow Management Portal.
- Navigate to Dynamic PKI > Certificate Authorities.
- Select the Intermediate CA created in Step 3, and then select the View icon under Functions.
- On the displayed page, scroll to the CRL section and copy the Base CRL URL.
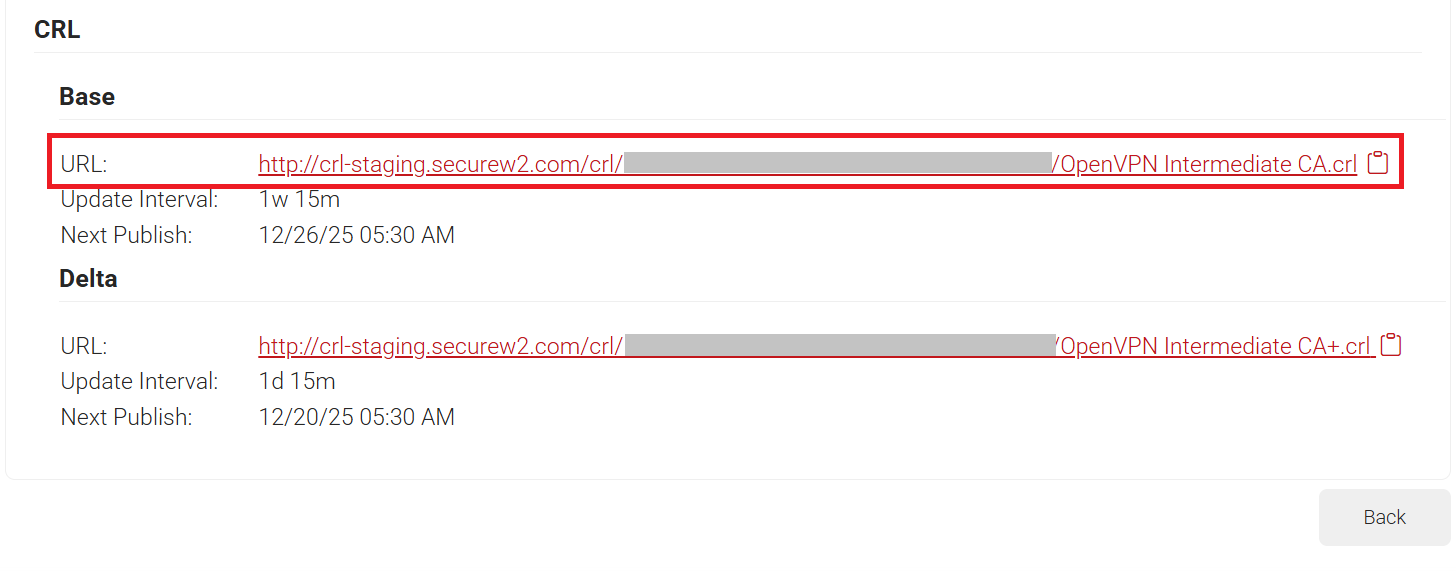
- Example: http://crl.securew2.com/crl/abcde12345/OpenVPN Intermediate CA.crl
Note: SecureW2’s Base CRL updates on a default one-week interval. This means newly revoked certificates aren’t reflected in the CRL until the next update cycle completes.
If your deployment requires more frequent updates, such as immediate revocation enforcement, contact SecureW2 Support to request a shorter CRL update interval.
2. Download and load the CRL
- Connect to your Access Server console and get root privileges.
- Download the CRL and save it in PEM format:
wget http://crl.securew2.com/crl/abcde12345/'OpenVPN Intermediate CA.crl' -O /root/crl.pem - Load the CRL into Access Server:
sacli --key "vpn.server.crl" --value "/root/crl.pem" ConfigPut sacli start
3. Confirm CRL enforcement
Once the CRL is active:
- Any client connecting with a revoked certificate is denied access.
- Any already-connected client whose certificate appears in the CRL is disconnected automatically.
- Future CRL updates are detected and applied automatically according to the resample interval (vpn.server.crl_resample).
NOTE: CRL is supported in OpenVPN Access Server version 3.0.0 and later. If you are using an older version, upgrade to the latest version.