Key Points
- PKIaaS is a cloud-based service that simplifies and modernizes PKI management, eliminating the need for on-premise infrastructure.
- PKIaaS offers enhanced scalability, rapid deployment, and simplified management by offloading complex tasks to a service provider.
- PKIaaS improves security and efficiency through automation of critical processes like key and certificate lifecycle management.
Public Key Infrastructure (PKI) keeps data secure, authenticates identities, and ensures end-to-end encryption. It plays a vital role in securing digital communications and involves a set of roles, policies, hardware, software, and procedures needed to create, manage, distribute, use, store, and revoke digital certificates. Essentially, PKI helps safeguard data and ensure secure communications.
Managing PKI in-house can be daunting, requiring significant resources and expertise. PKI-as-a-Service (PKIaaS) offers a solution to this. PKIaaS is a cloud-based solution that simplifies the complexity by providing private PKI functionalities as a service, eliminating the need for on-premises infrastructure. PKIaaS makes robust security accessible even to organizations that lack extensive IT departments.
This article defines what PKIaaS is, how it works, its core components, and the benefits it offers.
What Is PKI-as-a-Service (PKIaaS)?
PKI-as-a-Service (PKIaaS) is a cloud-based solution that delivers full Public Key Infrastructure (PKI) functionality, eliminating the necessity for on-premises infrastructure. This managed service encompasses seamless key generation, certificate management, and automation processes, all hosted on secure cloud environments. With PKIaaS, organizations can ensure robust cryptographic security and streamlined management, while benefiting from scalability, cost-efficiency, and enhanced compliance with security protocols.
How PKIaaS Differs From On-Premise PKI
PKI-as-a-Service (PKIaaS) offers several distinct advantages over traditional on-premise PKI, primarily through its cloud-based architecture and managed service model. PKIaaS differentiates itself in these ways:
- Infrastructure Management: On-premises PKI requires significant hardware and software installations and ongoing maintenance, whereas PKIaaS leverages cloud infrastructure, eliminating the need for physical equipment and reducing maintenance overhead.
- Scalability: Traditional PKI systems are often rigid, requiring substantial effort to scale. PKIaaS, hosted in the cloud, offers seamless scalability, allowing organizations to adjust to fluctuating demands easily.
- Deployment Speed: Setting up an on-premises PKI can be time-consuming, often spanning weeks or months. PKIaaS, thanks to pre-configured cloud environments, enables rapid deployment, often within hours.
- Certificate Outage Prevention: With traditional PKIs, renewal tracking for individual certificates can be complex and time-consuming. PKIaaS provides more visibility while introducing renewal and revocation automation to reduce risk.
- Automation and Integration: Traditional PKIs don’t offer much in the way of automation, custom scripting, or Application Programming Interface (API) compatibility. PKI-as-a-Service providers prioritize automation and APIs for smooth customization and integration.
- Security and Compliance: In-house PKIs are only as secure and compliant as your staff knows how to be. PKIaaS providers feature built-in, standardized security features for improved compliance with regulatory requirements, protection against data breaches, and disaster recovery assistance.
- Cost Structure: On-premises PKI typically involves substantial upfront and ongoing hardware, software, and personnel costs. PKIaaS operates on a subscription model, spreading costs over time and eliminating the need for large capital investments.
- Management Complexity: Managing a PKI in-house requires specialized expertise and constant oversight. PKIaaS offloads this burden to the service provider, simplifying management and ensuring that best practices in security and compliance are continuously followed.
Core Components of PKIaaS
PKIaaS encompasses several core components essential for robust cryptographic security and streamlined security management solutions. These include:
| Cloud Hosting | PKIaaS leverages cloud infrastructure to host the PKI, eliminating the need for physical hardware and ensuring high availability, redundancy, and disaster recovery. This also facilitates rapid scaling and resource optimization. |
|---|---|
| Automation | Automation in PKIaaS covers key generation, digital certificate issuance, renewal, and revocation. These automated processes drastically reduce the risk of human error and ensure timely updates, maintaining the integrity and security of digital signatures and encrypted communications. |
| Managed Services | PKIaaS offers managed services, including setup, ongoing maintenance, and support. These services ensure private keys, digital certificates, and cryptographic algorithms are properly configured and maintained, providing end-to-end encryption and secure communications. |
| Security Protocols | Robust security protocols are foundational to PKIaaS. It incorporates asymmetric cryptography, ensuring that public and private keys facilitate secure key exchange and data encryption. Advanced security measures protect against man-in-the-middle attacks and unauthorized access. |
| Certificate Management | Efficient certificate management is crucial. PKIaaS manages the lifecycle of digital certificates, ensuring proper issuance by trusted certificate authorities (CAs): organizations that serve as the official governing administrator of digital certificates. PKIaaS also handles automated renewal and revocation of certificates to maintain a secure connection and prevent vulnerabilities. |
| Authentication and Authorization | PKIaaS provides robust authentication mechanisms, utilizing certificates to verify identities during communication sessions and granting appropriate access based on predefined security policies. |
How PKIaaS Works
PKIaaS works by delivering the following:
Public Key Cryptography
Public key cryptography ensures secure key management, exchange, and encryption. This cryptographic technique employs a pair of public and private keys.
Public Key
The public key is openly distributed and used to encrypt data. Though freely accessible, it is a crucial part of the asymmetric encryption. It transforms plain text into an encrypted format that can only be deciphered by the matching private key. This ensures that even if the encrypted data is intercepted, unauthorized entities cannot read it.
Private Key
The private key is closely guarded and never shared. It works in tandem with the public key to decrypt information encrypted by the public key. The security of the entire system hinges on keeping the private key confidential. Only the private key holder can decrypt the messages and data, ensuring robust security.
Importance of the Public and Private Keys for Data Integrity and Confidentiality
Public and private keys are essential for maintaining data integrity and confidentiality. When encrypted using a public key, only the corresponding private key can decrypt data. This guarantees that the data remains intact and unaltered during transmission, preventing attacks. Digital signatures’ integrity is similarly maintained, providing proof of data authenticity and origin.
Certificate Lifecycle Management (CLM)
PKIaaS streamlines certificate lifecycle management (CLM), automating digital certificate issuance, renewal, and revocation process. Trusted certificate authorities oversee the issuance of certificates, ensuring their validity and trustworthiness. Automated renewal prevents expired certificates from compromising security, and revocation ensures compromised or invalid certificates are promptly invalidated. This full lifecycle management ensures continuous security compliance and minimal operational disruption.
PKI vs. SSL
PKI provides the infrastructure (CA, RA, etc.) to enable CLM. Together, they contain everything an organization needs to issue, store, renew, revoke, and otherwise manage digital certificates.
Secure Sockets Layer (SSL) is one component of CLM: a security protocol used to pass encrypted communications between browsers and servers. Today, most organizations use a modernized form of encryption called Transport Layer Security (TLS), though “SSL” is still the common industry term for both protocols.
Authentication and Authorization
Authentication and authorization are critical aspects of PKIaaS. PKIaaS ensures that entities are authenticated before accessing sensitive data or systems. This authentication process verifies the identity of users and devices, ensuring that only authorized entities have access.
PKIaaS also enforces authorization policies, granting access rights based on predefined security rules. This combination of robust authentication and precise authorization fortifies overall security, ensuring secure communications and data integrity across all interactions.
Is PKI an AAA (Authentication, Authorization, Accounting) Protocol?
No, PKI isn’t an Authentication, Authorization, Accounting (AAA) protocol.
The AAA framework is a network access control (NAC) protocol for transmitting sensitive data, particularly over wireless networks. AAA servers help routers securely authenticate (verify user credentials), authorize (allow access), and account (record user/access details) all attempts to access the network.
Traditional and cloud-based PKIs provide authentication for certificate requests by verifying the identity of users and devices. They also authorize access once authenticated.
Traditional PKIs don’t provide robust built-in accounting — a critical security measure. However, many managed PKI service providers, including the SecureW2 JoinNow Platform, include accounting for improved security, compliance, and audit management.
Benefits and Advantages: Why Businesses are Ditching On-Premises PKI Over PKI-as-a-Service
Businesses are increasingly transitioning from on-premises PKIs to PKI-as-a-Service due to the numerous advantages that PKIaaS provides. Some key benefits driving this shift include:
Cost Efficiency
Traditional PKI systems demand significant capital investment in hardware security modules, software, and specialized personnel for management. PKIaaS operates on a subscription-based model, spreading costs over time and eliminating hefty upfront expenses. This makes robust PKI accessible to businesses of all sizes.
Scalability
On-premises PKI solutions are often rigid and require substantial effort to scale. PKIaaS leverages cloud infrastructure, providing seamless scalability that allows businesses to adapt quickly to growing or fluctuating demands. Known as crypto agility, this elasticity ensures enterprises can scale their cryptographic key infrastructure without overcommitting resources.
Complete Visibility
When including a comprehensive CLM solution, PKI-as-a-Service providers can offer total visibility into all issued certificates: full details, logs, expiration dates, and more. Automation simplifies management, so you don’t have to access these details as often as you might with a traditional PKI. Still, transparent visibility augments regulatory compliance, renewals, and revocations.
Enhanced Security
PKIaaS providers adhere to strict enterprise security protocols, ensuring optimal cryptographic keys and digital signature protection. Features such as automatic key generation, certificate issuance, and renewal offer stronger security measures. Asymmetric encryption used in PKIaaS ensures that only the matching private key can decrypt messages encrypted with the public key, safeguarding data integrity.
Built-in Compliance
Many managed PKI services include automated accounting: logs or records of all access decisions for your issued certificates. By tracking critical data, including device posture, user identity, policy decisions, and potential risk factors, you get a detailed trail to meet compliance and audit requirements — all with less manual reporting for your team.
Simplified Management
Managing an on-premises PKI system requires constant oversight and specialized expertise. PKIaaS simplifies this by providing managed services where the service provider takes care of all operational tasks, including key management, certificate authority functions, and compliance with industry standards. This offloading allows IT departments to focus on core business functions.
Rapid Deployment and Integration
Thanks to preconfigured cloud environments, PKIaaS offers near-instant deployment compared to the time-consuming setup of on-premise systems. Furthermore, PKIaaS integrates smoothly with existing infrastructure, supporting various out-of-the-box applications and devices. This flexibility ensures businesses can quickly enhance their security posture without extensive modifications.
Common Challenges with PKIaaS
Managed PKI services aren’t a magic solution to every problem. Be mindful of these risks and disadvantages:
- Incompatibility with Legacy PKI Infrastructure Management Practices: Moving from traditional PKI to PKI-as-a-Service isn’t just a system change — it’s a process change, too. For many organizations, the transition requires operational updates, which can prolong implementation.
- Unclear Responsibility: Along with procedural changes, implementing PKIaaS also requires a review of governance policies and ownership among teams. It’s critical to establish who owns intra- and inter-departmental approvals along with how to enforce new policies, and who enforces them. Don’t just define ownership. Document it.
- Automation without Customization: PKIaaS platforms provide a wealth of certificate automations designed to reduce manual work, minimize human errors, improve efficiency, and meet or exceed compliance requirements. But standard configurations can’t do it all. Personalize details like certificate lifetimes, trust policies, key sizes, and revocation practices to match company and industry standards.
In addition to your in-house PKI experts, lean on your PKIaaS provider to help streamline implementation, maximize personalization, and guide essential policy and governance updates.
When To Use PKI-as-a-Service
A managed PKIaaS solution may be right for your organization if you manage:
- Distributed Workforces: Across multiple facilities and remote teams, many organizations trust managed PKI services for secure network access.
- High Volumes of Digital Certificates: Managed PKI is perfect for organizations with an extensive number of certificates, which would ordinarily require significant oversight.
- Rapid Certificate Issuance Needs: For teams that need to issue certificates on demand, PKIaaS can streamline the process without compromising compliance.
- Myriad Internet of Things (IoT) Devices: With hundreds, thousands, or even millions of IoT devices comes a need for individual device validation. At this scale, manual device management isn’t realistic, but PKI-as-a-Service can provide certificate security for IoT devices.
- Teams Without Sufficient PKI Experts: Without an appropriate number of specialized, highly trained staff members, you won’t have the resources to handle the complexities of traditional PKI in-house.
- Low-Budget Infrastructure: Traditional PKIs require expensive hardware and infrastructure: on-premise data centers, hardware security modules (HSMs) to store and manage keys, load balancers, maintenance staff, and more. PKIaaS solutions typically offer lower costs.
For reliable, efficient, secure PKI infrastructure, consider PKI-as-a-Service.
How To Migrate from Legacy PKI to PKIaaS
PKIaaS offers rapid deployment, but preparation is key. Follow this process for simplified implementation, onboarding, and long-term success.
Start with a discovery process to map out all PKI processes, along with current root CAs, issuing CAs, certificate profiles, and expiration dates. Include all teams in this exercise, since this is also the best time to identify and document manual processes and unspoken policies.
Next, identify target use cases to test in your new PKI architecture. To avoid major disruptions, choose low-risk certificate types and test simultaneously on both your legacy system and new platform.
When you’re ready to transition, be smart! This will be a gradual process. Issue new certificates through your new managed service while keeping legacy certificates on your legacy platform. One by one, expired certificates will renew on your new platform until the transition is complete.
Once initial implementation, testing, and troubleshooting is complete, increase automation and continuous monitoring processes to reduce (but not eliminate) manual oversight. Automation can’t completely replace human inspection, nor should it — but over time, it should simplify the process. That’s especially true with managed services, where a team of PKI experts helps manage the workload.
Finally, when no legacy certificates remain, you can prepare to decommission your legacy PKI servers. While delicate, this final step improves security while reducing operational costs, so don’t skip it.
Enhance Your Security Posture with SecureW2’s Managed PKI
Transitioning from traditional on-premise PKI to a managed PKI solution can drastically enhance your organization’s security posture. The SecureW2 JoinNow Connector PKI offers a comprehensive managed PKI solution that seamlessly integrates with existing infrastructure to deliver robust functionalities.
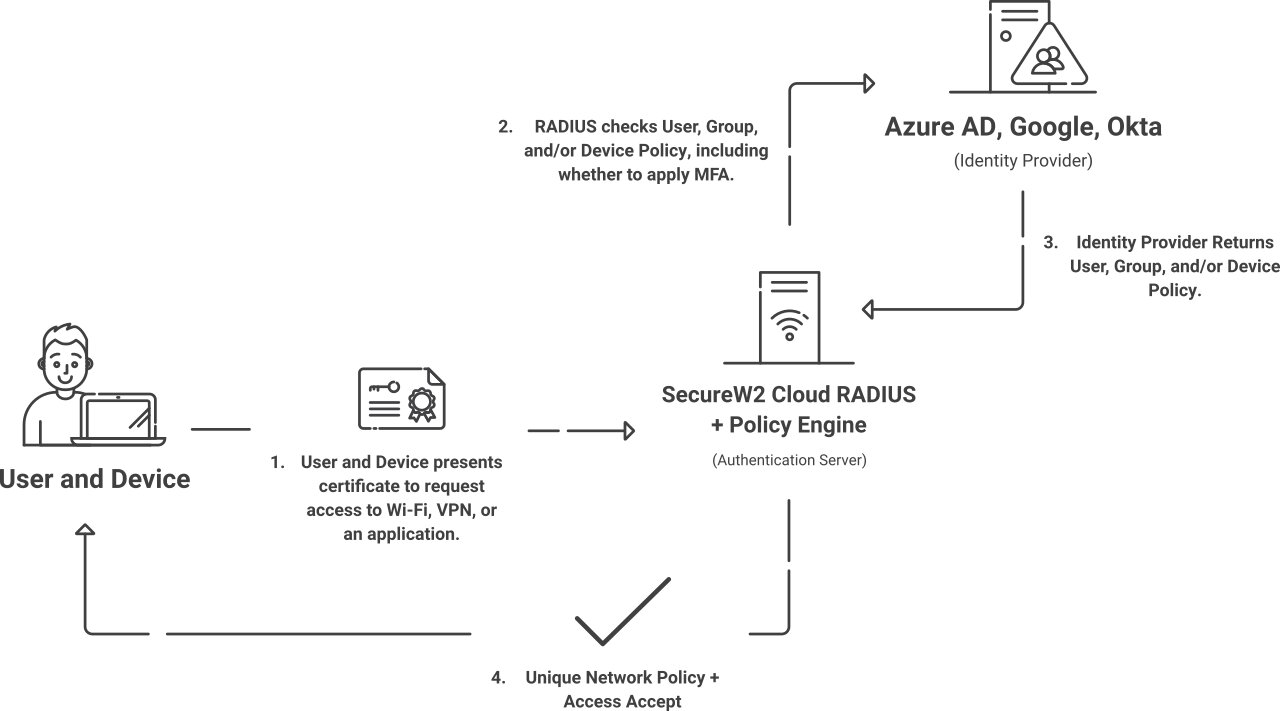
The SecureW2 managed PKI solutions are designed with scalability, security, and simplicity. By leveraging SecureW2 cloud-based services, including Cloud RADIUS, organizations can streamline certificate management, automate the issuance of digital certificates, and enhance secure communications through advanced public key encryption. This combination simplifies the onboarding process for users and devices and significantly reduces operational costs by eliminating the need for on-premise hardware security modules and specialized personnel.
Our Cloud RADIUS enables secure authentication and authorization, ensuring only authorized users can access sensitive data and resources. With features like automatic key generation, digital signatures, 802.1X authentication, and certificate authority functions, our PKI solutions provide an added layer of security that protects against man-in-the-middle attacks and unauthorized access. By choosing SecureW2, businesses can enjoy peace of mind from a highly secure and efficient public key infrastructure tailored to meet the demands of modern digital environments.
Ready to upgrade your security infrastructure? Explore the benefits of the SecureW2 JoinNow Connector PKI and Cloud RADIUS to see how a managed PKI solution can transform your organization’s approach to security, simplify management, and save costs. Request a free demo today to learn more and take the first step towards a more secure, streamlined future.
