Key Points
- Digital certificates add an extra layer of security to a network, but if invalid certificates are not revoked on time, they could make your network vulnerable to attacks and infiltration attempts
- Challenges in certificate management arise from manual processes, such as manually revoking certificates, which increase the risk of security gaps and operational inefficiencies.
- Automated certificate lifecycle management simplifies operations and improves security, especially in complex IT environments.
Imagine conducting important business online without identifying the person you’re interacting with. It would be like handing sensitive documents to a stranger on the street; every login would be risky. Fortunately, internet protocols exist to build trust in the digital world, with one of the most important being the public key infrastructure (PKI) certificate.
In this blog post, we’ll take a closer look at PKI certificates, explaining what digital certificates are, why they matter, and how you can obtain them easily to safeguard your online activities.
What Is a Public Key Infrastructure Certificate?
A public key infrastructure certificate (PKI certificate) is a digital document that serves as a means of verified identification, similar to a driver’s license or passport. Certificates identify an entity (person, device, or service) online. This allows you to verify you’re dealing with the correct person and securely communicate with them.
PKI certificates rely on a complex cryptographic system known as asymmetric cryptography. The basic concept is relatively straightforward. Consider a specialized lock featuring two distinct keys: the public and private keys.
Anyone can access a public key. It’s used to encrypt data, and there’s no risk in sharing it because you can’t decrypt data without your own private key. Only you know the private key, and it’s never transmitted during verification. That’s why this approach is called asymmetric cryptography, because you can’t use the same key to both encrypt and decrypt the data.
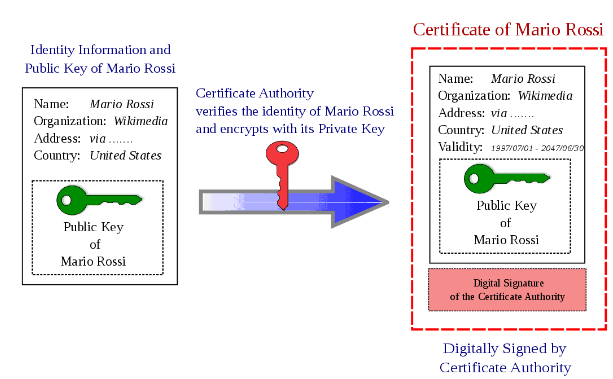
A PKI certificate acts like a digital certificate of ownership for your public key, issued by a trusted entity known as a certificate authority (CA). The CA serves as a verifier, attesting to the public keys and the authenticity of the entity holding the certificate.
The certificate binds your public key to your identity, providing verification for subsequent digital signatures and other identification processes. PKI certificates include details such as the holder’s name, organization (if applicable), and the duration of the key’s validity.
PKI certificates are increasingly popular and widely used, especially as SSL certificates for secure online browsing. According to BuiltWith, there are more than 93 million SSL certificates on the internet as of May 2026.
PKI certificates are also called digital certificates and X.509 certificates. Organizations use them in place of traditional credentials to secure networks, emails, digital signatures, and more.
Advantages of PKI Certificates
PKIs deliver the following benefits:
Secure Communication (Encryption)
A PKI or a digital certificate enables the use of encryption, a process that scrambles or encrypts data into an unreadable format. This ensures that even if someone checks in on your conversation, they can’t decipher the information.
Websites with legitimate SSL/TLS certificates display a padlock icon on the browser’s address bar to indicate that a connection is secure. This protects sensitive data, including login credentials and financial information, during transmission.
User/Device Authentication Using Digital Certificates
Digital certificates authenticate the identity of users and devices that are attempting to access a network or online resource. This measure protects against unauthorized access and malicious entities.
Data Integrity (Digital Signatures)
PKI certificates can digitally sign both documents and emails. This guarantees the integrity of the data during transmission, enables the recipient to authenticate the sender’s identity, and offers non-repudiation (prevents the signer from disputing their signature).
Simplified Identity Management
Many PKI authentication services feature automated certificate lifecycle management. This means issuance, renewal, and certificate revocation don’t require extensive manual effort.
And on the end entity’s side, while secure credential management usually requires users to change passwords regularly, PKI certificates don’t have the same requirement.
Brand Trust and Credibility
Some types of PKI certificates instill more trust in a brand, especially when it comes to protecting sensitive data. For example, when organizations use SSL/TLS certificates to secure their site with HTTPS, users can feel confident that they’re visiting the intended site. This is crucial when providing personal info for e-commerce transactions, financial services, or healthcare.
Interoperability and Scalability
PKI systems and certificates integrate with many modern software and platforms. This enables easy deployment without major changes to your existing infrastructure. PKI is also highly scalable, especially when using managed cloud PKI services. Services like this make it simple to add more users and certificates as your organization grows.
Common Use Cases and Industries for PKI Certificates
Here are several common reasons organizations use digital certificates, including some of the challenges PKI solves:
- Secure web browsing with SSL/TLS certificates: SSL/TLS certificates provide HTTPS connections that show users they have a certified connection to a legitimate website, not a spoofed site.
- Verified digital signatures on documents and software: PKI certificates provide non-repudiation: a digital footprint for verifiable, indisputable signatures. This is important because certificate signing can be cumbersome, and bad actors can forge handwritten signatures.
- Secure connections to private networks: Organizations use PKI certificates to protect wired and wireless networks, including intranets and virtual private networks (VPNs), by replacing user credentials with PKI certificates and secure network access protocols such as 1X authentication.
- Sensitive data encryption and communication: PKI certificates help transmit data via email or secure networks without fear of unverified users gaining access.
- Unmanaged devices and IoT: Organizations with bring-your-own-device (BYOD) policies and internet of things (IoT) devices need reliable security controls. PKI authentication helps protect against hackers and other unauthorized access.
- Avoiding MITM attacks: Man-in-the-middle (MITM) attacks occur when hackers intercept data during transmissions between client and server. But if the hacker doesn’t have the private key, they can’t decrypt the information.
PKI certificates are ideal for industries with strict regulatory requirements governing user authentication and secure communication. That includes:
- Large or dispersed organizations (intranets, VPNs, email encryption)
- Financial institutions (online banking)
- Physical and online retail (IoT devices and e-commerce software)
- Local and federal government agencies (identity verification and digital signatures)
- Healthcare (electronic health records and HIPAA compliance)
Challenges and Risks of PKI Certificates
Public key infrastructure comes with some challenges to be aware of.
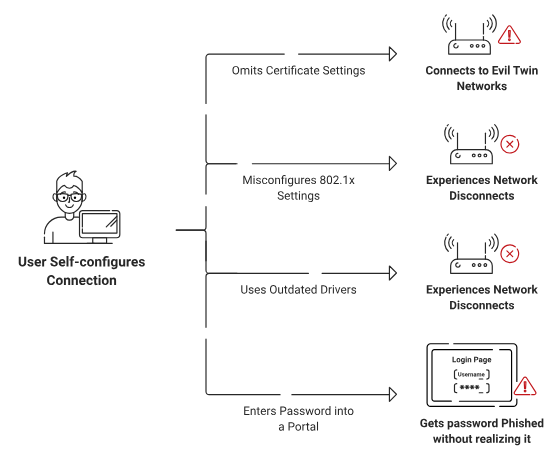
Digital certificates go hand-in-hand with certificate lifecycle management (CLM). When you issue certificates without proper verification processes, let valid certificates expire without renewal, or spend too much time managing certificates manually, you’re susceptible to infiltration.
Also, while your certificate authorities should be trusted third parties, not all CAs are trustworthy. Without proper certificate policy management, CAs can let hackers in, leaving your organization, data, and users vulnerable. Choose your certificate authorities carefully.
What Is Certificate Lifecycle Management?
Certificate lifecycle management refers to the processes involved in managing digital certificates from creation through retirement. It covers the full lifecycle of a certificate, including:
- Issuance and enrollment of certificates to users, devices, or servers
- Provisioning and deployment
- Monitoring expiration dates and automated renewal
- Revocation of compromised or no-longer-needed certificates
- Reporting, auditing, and maintaining visibility across all certificates
Without effective certificate lifecycle management, organizations often experience costly downtime from expired certificates, security vulnerabilities from slow revocation, and significant manual effort.
Modern managed PKI solutions solve these problems through automation and seamless integration with MDM and identity directory services. This greatly reduces risk and operational burden compared to traditional manual or self-managed PKI approaches.
Different Types of PKI Certificates
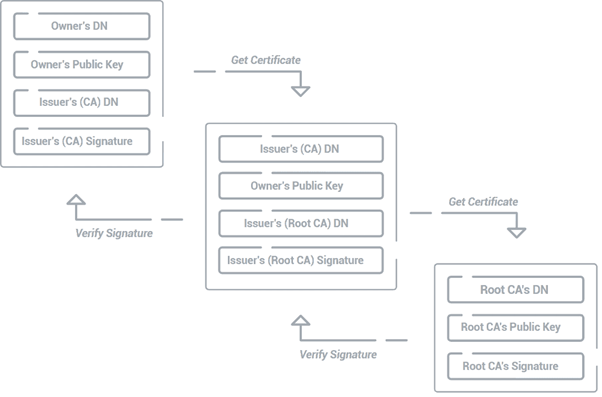
Depending on their origin and destination, digital certificates are either trusted root certificates (the self-signed certificate directly from a root CA), intermediate/issuing certificates (signed by root CA and used to issue end-entity certificates), or end-entity/leaf certificates (signed by intermediate CA and issued directly to users).
The order in which CAs issue these digital certificates is called a trust chain or certificate chain. This chain of trust verifies signatures against the issuing CA’s public key, linking entities to a trusted root CA.
Common categories of PKI certificates include:
- Client certificates to identify users or devices
- Document signing certificates to provide irrefutable digital signatures
- Code signing certificates for developers to sign software for integrity
- Email certificates to encrypt and sign emails, also known as Secure/Multipurpose Internet Mail Extensions (S/MIME)
- SSL/TLS certificates to secure communications between web servers and clients
There are other highly specific types of certificates for domains and browsers, too. You can choose which certificate types to issue based on how many domains you need to cover, how you want them certified (individually or in groups), and what level of trust you require.
How Does a PKI Certificate Work? Symmetric Encryption and Asymmetric Encryption
To understand how PKI certificates work, you need to know how symmetric and asymmetric encryption work.
PKI certificates work through asymmetric encryption, which means you use cryptographic keys with different access levels to encrypt (public key) and decrypt (private key) your message. This is also known as public key encryption.
The alternative is symmetric encryption, where you use the same key to encrypt and decrypt. While using a single key was common in the past, it is less widely used today because it is not as secure as asymmetric encryption.
The classic Bob-Alice example is a helpful analogy.
In symmetric encryption, Bob and Alice use a locked trunk to exchange private messages. They share the same key to unlock the trunk, and the trunk can be in one of two possible states: locked or unlocked. That’s symmetric encryption.
In asymmetric encryption , the lock requires two distinct encryption keys. Only the public key turns to the left (encrypts) while only the private key turns to the right (decrypts). And instead of two simple states (locked/unlocked), there are now three different states for the trunk to be in:
- Turned to the left with a public key: Locked
- Key in the middle: Unlocked
- Turned to the right with a private key: Locked
Both keys can lock the trunk — but once someone has turned it, you need the other key to turn it back.
Now, Alice can pick a private and public key, sharing the public key with Bob. Bob can put messages (plaintext data) in the trunk and use Alice’s public key to encrypt messages by locking to the left, knowing Alice will have to use her private key to turn the lock back and retrieve the message.
Alice can then put a response in the trunk and then use her private key to turn it all the way to the right. If Bob comes back and sees the lock turned to the right, he knows Alice was the one to send the message — since only her private key moves the lock in that direction.
How to Get a PKI Certificate
There are two primary methods for obtaining a PKI certificate, each suited for different needs:
Purchase From a Certificate Authority
The most common strategy for securing websites and applications is through purchasing a PKI certificate from a CA. Known CAs provide different types of PKI certificates based on your specific needs. SSL certificates are commonly used to encrypt website traffic while code signing certificates are used to authenticate software downloads.
Pros:
- Easy and convenient: CAs provide streamlined purchasing and issuance processes.
- Wide variety of certificates available: CAs provide different certificate types to match specific security needs.
- Cost-effectiveness: CAs offer affordable options for standard website encryption and authentication requirements.
Cons:
- Limited control: CAs retain control over certificate issuance and lifecycle management processes.
- Ongoing renewal costs: CAs enforce certificate expiration and require periodic renewal fees.
Construct a Self-Built PKI
Optionally, some organizations choose to construct their own public key infrastructure by using resources such as Microsoft’s Active Directory Certificate Services (AD CS).
While offering greater control, building your own PKI requires significant resources and expertise. This process requires hardware, the physical space to store that additional hardware, and the ability to maintain it regularly. Here is an overview of the advantages and disadvantages of this option:
Pros:
- Maximum control: You have complete control over PKI issuance, management, and security policies.
Cons:
- High cost: You require significant investment in hardware, software, infrastructure, and PKI expertise to maintain certificates.
- Management complexity: You must manage certificate enrollment, issuance, renewal, and revocation processes, which are complex and time-consuming without automation.
- Scalability challenges: You must invest significant resources to scale PKI infrastructure to meet growing organizational needs.
- Geographical limitations: You must duplicate PKI infrastructure across multiple locations if your organization operates at more than one site, increasing complexity and costs.
Issue Certificates With a Managed PKI Service
Managed PKI services provide a cloud-based solution for issuing and managing PKI certificates within your organization. Managed PKI services like SecureW2 JoinNow Dynamic PKI offer a cloud-based solution that streamlines issuing and managing PKI certificates within your organization. It makes it easier than ever to secure your digital environment.
Here’s a quick cost comparison between a managed PKI solution like Dynamic PKI and building your own:
Dynamic PKI eliminates the need to replicate the infrastructure at different office locations. Additionally, it does not require building from scratch, so organizations can enjoy swift deployment and reduced costs. This approach simplifies the process compared to building your own PKI infrastructure and offers a variety of beneficial features.
Pros:
- Increased control: Organizations maintain centralized control over certificate issuance and management while using a managed cloud service.
- Scalability: Organizations support growing security and device management needs without building on-premises PKI infrastructure.
- Simplified deployment: Organizations reduce operational complexity by using managed services to handle certificate lifecycle processes.
Cons:
- Initial setup complexity: Organizations require technical expertise to configure and integrate the managed PKI service into their environment.
- Higher initial cost: Organizations incur higher upfront costs compared to basic certificate authority solutions for simple use cases.
How Does Certificate Issuance Work With Managed PKI?
Requesting and obtaining PKI certificates can be a seamless process. Our managed PKI service makes this a reality. We simplify certificate issuance in two different ways, depending on whether you are issuing certificates to a company-owned, managed device or an unmanaged device/BYOD.
We offer managed device gateways for devices managed by MDMs such as Intune. Using the Simple Certificate Enrollment Protocol (SCEP), these gateways integrate with your MDM platform and automatically issue certificates to all endpoints. With Intune and Jamf Pro, we can also automatically revoke certificates based on the groups you create in your MDM.
With BYODs, we offer a simple onboarding application called JoinNow MultiOS. All end users need to do is navigate to your customized onboarding landing page and run the application. It empowers them to configure their own devices and request certificates in less than a minute.
By automating workflows and offering user-friendly onboarding solutions, SecureW2 removes the complexity associated with traditional PKI management. This allows your IT team to focus on more strategic initiatives while ensuring a strong foundation of trust within your organization’s digital environment.
SecureW2: A Managed PKI Platform to Easily Issue Digital Certificates
Public key certificates offer secure communication, which is a necessity for online security. Each entity must thoroughly understand the procedures involved in obtaining these digital credentials.
Implementing a managed PKI service, such as Dynamic PKI, offers multiple benefits, including a streamlined issuance procedure, reduced administrative workload, enhanced scalability, and an improved security posture. BYOD compatibility and MDM integration facilitate the integration of a wide range of device ecosystems, whereas our intuitive platform automates certificate enrollment and streamlines the onboarding procedure.
By utilizing SecureW2, users can effectively manage the financial implications of internal PKI certificates and identify a solution compatible with their organizational budget. SecureW2 is dedicated to providing the necessary knowledge and resources to establish a reliable and safe digital environment. Schedule a free demo to learn more!
Frequently Asked Questions
What Is a PKI Certificate?
A PKI certificate is a digital document used to verify the authenticity and integrity of electronic communications. It contains information such as the owner’s identity, a public key, and a digital signature, which are used to secure communication over networks.
Where Can I Get a PKI Certificate?
You can acquire PKI certificates from a CA or through your own PKI, either by using a managed service or building it yourself.
How Do You Create a PKI Certificate?
Certificates can be issued via public CAs (like Sectigo, Digicert, etc) or private ones. With a public CA, the process begins by generating a key pair (public and private) on your device. You then submit a certificate signing request (CSR), which includes your public key, to the CA. The CA verifies your identity and, once validated, issues a certificate that links your public key to your verified identity. In a private PKI setup, the steps are similar, but the validation is handled internally rather than by a public authority. This may involve enrolling through a managed service or requesting a certificate within a self-built PKI environment. After internal validation of the user, device, or system, the PKI infrastructure issues the certificate. Managed PKI services generally make this process more streamlined and easier to maintain compared to building and managing a PKI system from scratch.
How Much Does a PKI Certificate Cost?
The costs for certificates can differ based on factors such as the type of certificate, the chosen CA, and the specific plan you choose for managed PKI services.
Who Issues PKI Certificates?
Certificate authorities, the trusted entities for digital certificate issuance, issue the majority of PKI certificates. Organizations can create their own PKI to internally issue certificates, which can be facilitated by a managed PKI service. A chain of trust is established at each layer of the PKI, with root certificates at its core.
How Do I Get My PKI Certificate?
The method depends on where you obtain it. Through a CA, you typically purchase and download it. A managed PKI service often automates the process upon user enrollment.
Why Do I Need a PKI Certificate?
PKI certificates offer several benefits: secure communication (encryption), user/device authentication, and data integrity (digital signatures). They create a foundation of trust online.
What Is PKI and Certificate Management?
PKI is a system for issuing and managing PKI certificates. Management involves tasks like enrollment, renewal, and revocation.
What Is PKI Certificate Authentication?
The authentication of public key infrastructure certificates involves the verification of a PKI certificate’s validity by the issuing CA. This verifies the identity of the entity to which the certificate belongs.